 The tension in the Middle-East apparently prompted a game-changing move by the U.S. President. Washington Post sources say exactly 10 years after Stuxnet, the President approved a cyberattack that took down Iranian missile control computers on the night of June 20th. The exact impact of the Cyber Command operation isn't clear, but it was described as "crippling".
The tension in the Middle-East apparently prompted a game-changing move by the U.S. President. Washington Post sources say exactly 10 years after Stuxnet, the President approved a cyberattack that took down Iranian missile control computers on the night of June 20th. The exact impact of the Cyber Command operation isn't clear, but it was described as "crippling".
The Wall Street Journal reported that Iran may attempt to retaliate with spear phishing strike back attacks against the U.S. if the tension in the Middle East continues to escalate.
Researchers at FireEye and CrowsStrike have spotted phishing campaigns linked to a known Iranian hacking group that possesses powerful, destructive tools like the Shamoon disk-wiper that was recently used to attack Saudi Government targets and literally destroyed 35,000 machines at Saudi Aramco in 2012.
The Department of Homeland Security's cyber-security agency is warning of increased cyber-activity from Iranian hackers, and urging US companies to take protective measures against these hacker groups' most common practices -- the use of data-wiping malware, credential stuffing attacks, password spraying, and spear phishing. The warning was published in a tweet by the Cybersecurity and Infrastructure Security Agency (CISA) Director Christopher Krebs.
CrowdStrike said the targeting appeared focused on U.S. government and energy-sector entities, including oil and gas, and that it had seen email lures posing as messages from the White House’s Executive Office of the President.
Adam Meyers, CrowdStrike’s vice president of intelligence, said “They are going to potentially look for ways to retaliate in the event that there is an attack, and disrupting the global energy market would fall well within the area they see as appropriate."
Iranian hackers are seen as having a more limited ability to penetrate American critical infrastructure networks than Russia or China, a U.S. intelligence official said. But U.S. national security agencies are concerned, nonetheless, that Iran may seek to disrupt the power grid or other critical infrastructure if the hostilities persist, the official said.
IT pros did not sign up for this, but they are finding themselves in the trenches of a cyberwar that seems to be heating up consistently. Most bad actors go for the most available attack surface—your employees—with social engineering attacks. Make sure you step them through new-school security awareness training.
Will your users respond to phishing emails?
KnowBe4's Phishing Reply Test (PRT) is a complimentary IT security tool that makes it easy for you to check to see if key users in your organization will reply to a highly targeted phishing attack without clicking on a link. PRT will give you quick insights into how many users will take the bait so you can take action to train your users and better protect your organization from these fraudulent attacks!
 Here's how the Phishing Reply Test works:
Here's how the Phishing Reply Test works:
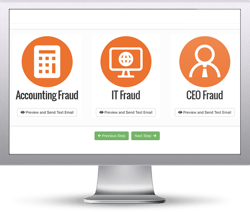
- Immediately start your test with your choice of three phishing email reply scenarios
- Spoof a Sender’s name and email address your users know and trust
- Phishes for user replies and returns the results to you within minutes
- Get a PDF emailed to you within 24 hours with the percentage of users that replied
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:





