
Payment fraud continues to soar, as a record 82 percent of organizations reported incidents in 2018, according to the 2019 AFP Payments Fraud & Control Survey, underwritten by J.P. Morgan.
Large organizations were particularly vulnerable to payments fraud, as businesses with revenue greater than $1 billion reported a jump of seven percentage points year-over-year to 87 percent. Organizations with revenue less than $1 billion experienced fewer fraud attempts in 2018, down four percentage points to 69 percent from 73 percent.
Business Email Compromise (BEC) also set a record. Eighty percent of companies reported BEC fraud last year, up from 77 percent in 2017. More than half (54 percent) of organizations reported financial losses as a result of BEC, the first time since AFP began tracking this data that this number climbed above the 50-percent mark. More than three-fourths of companies are responding by adopting stronger internal controls.
"Payments fraud is a persistent problem that is only getting worse despite repeated warnings and educational outreach," said AFP President and CEO, Jim Kaitz. "Treasury and finance professionals need to learn the latest scams and educate themselves—and perhaps more importantly—their work colleagues on how to prevent them."
"It is equally important for businesses to mitigate against non-financial implications of payments fraud," said Jessica Lupovici, Managing Director, J.P. Morgan. "Businesses stand to suffer reputational risk, which can be severe, expensive and require significant clean-up efforts."
Brand-New Tool: Phishing Reply Test Identifies Users Likely to Fall Victim to Fraudsters
Highly targeted phishing attacks, known as Business Email Compromise or CEO fraud scams have exceeded $12.5 billion in total known losses worldwide. These social engineering attacks are used by the bad guys to impersonate your CEO, CFO, or even third-party organizations you work with.
They convince your users, often in Accounting, HR, or even IT into making wire transfers or other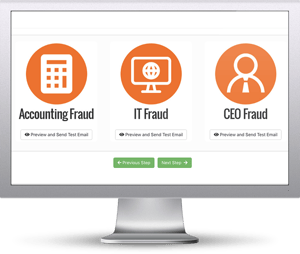 sensitive transactions because they “own” the keys to the kingdom. In fact according to a recent Barracuda report, 60% of pretexting email attacks do not involve any link. These attacks are clever because they bypass your traditional approaches to email security.
sensitive transactions because they “own” the keys to the kingdom. In fact according to a recent Barracuda report, 60% of pretexting email attacks do not involve any link. These attacks are clever because they bypass your traditional approaches to email security. Find out how many of your users take the bait and reply to a spoofed email.
KnowBe4’s Phishing Reply Test (PRT) is a new and complimentary IT security tool that makes it easy for you to check to see if key users in your organization will reply to a highly targeted impersonation attack. You’ll get quick insights into how many users will take the bait so you can take action to train your users and better protect your organization from these fraudulent attacks!
Here’s How the Phishing Reply Test works:
- Immediately start your test with your choice of three phishing email reply scenarios
- Spoof a Sender’s name and email address your users know and trust
- Phishes for user replies and returns the results to you
- Get a PDF emailed to you within 24 hours with the percentage of users that replied
Identify how many of your users take the bait...and reply to a spoofed email before the bad guys do!
Don't like to click on redirected buttons? Copy & paste this link into your browser:





