The Microsoft Threat Intelligence Center (MSTIC) has discovered that the SolarWinds hackers are behind an ongoing spear-phishing campaign targeting government agencies worldwide.
"This week we observed cyberattacks by the threat actor Nobelium targeting government agencies, think tanks, consultants, and non-governmental organizations," MSTIC revealed.
"This wave of attacks targeted approximately 3,000 email accounts at more than 150 different organizations.
"While organizations in the United States received the largest share of attacks, targeted victims span at least 24 countries."
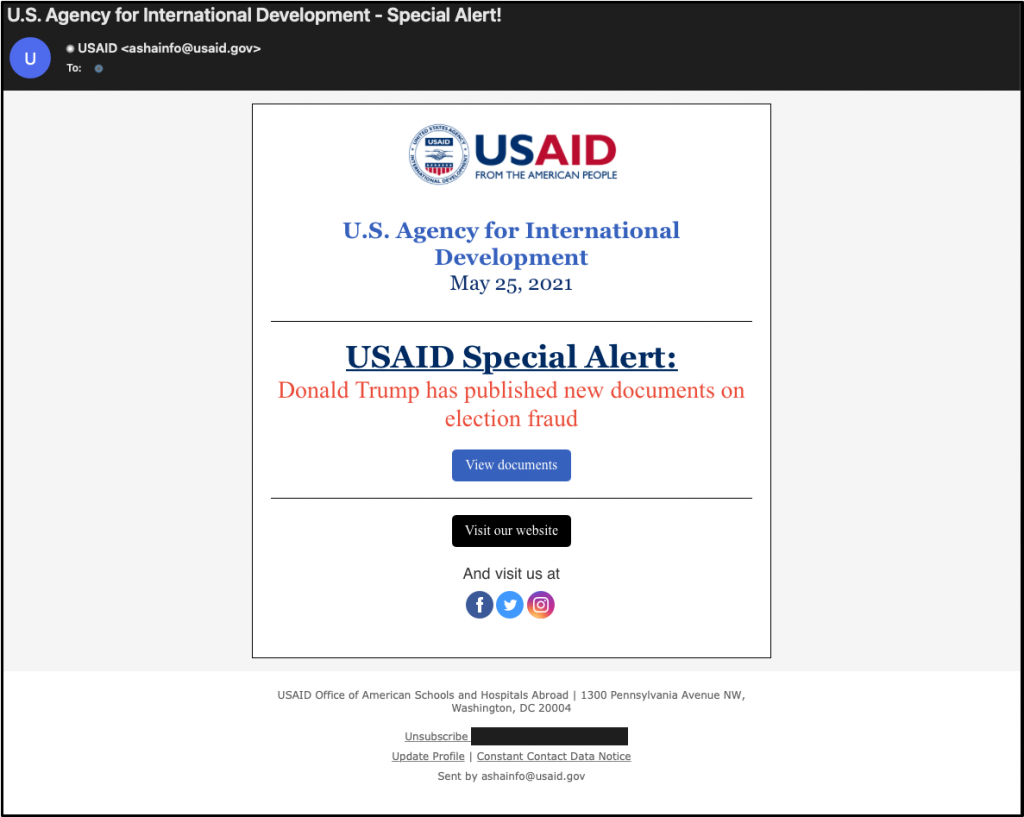
Phishing emails sent using hacked USAID email marketing account
The threat actors behind these attacks, a hacking group tracked as Nobelium by Microsoft and likely backed by the Russian government, sent the phishing emails using USAID's compromised Constant Contact account (a legitimate email marketing service).
The campaign started in January 2021, and it slowly turned into a series of attacks culminating with this week's USAID-themed phishing wave.
Cybersecurity company Volexity also published a report linking this phishing campaign with Russian Foreign Intelligence Service (SVR) operators (tracked as APT29, Cozy Bear, and The Dukes) based on tactics previously used in attacks going back to 2018.
Nobelium's infection chain and malware delivery techniques evolved throughout the attacks, with the spear-phishing messages containing HTML attachments dropping an ISO file onto the victims' hard drives.
After the victims mounted the ISO they were encouraged to open the files contained within (LNK shortcut or RTF documents), which would execute a DLL bundled withing document or stored within ISO image, loading Cobalt Strike Beacon on the system.
"If the device targeted was an Apple iOS device, the user was redirected to another server under NOBELIUM control, where the since-patched zero-day exploit for CVE-2021-1879 was served," Microsoft added.
More details, including the attackers' motivation, the malicious behavior observed by Microsoft during the attacks, and best practices to defend against this ongoing campaign, can be found in MSTIC's report.
The SolarWinds hackers
In December, the SolarWinds network management company was breached in a cyberattack that allowed the attackers to launch a supply chain attack targeting the company's customers.
SolarWinds advertised a select customer base including at least 425 organizations in the US Fortune 500 rankings, top ten US telecommunications companies, all US Military branches, the Pentagon, NASA, the NSA, the Postal Service, the Department of Justice, and the Office of the President of the United States.
SolarWinds revealed in March expenses of roughly $3.5 million through December 2020 from last year's supply-chain attack and is expecting high additional costs throughout the next financial periods.
The hacking group behind the SolarWinds supply-chain attack is tracked as Nobelium (Microsoft), NC245
Even though the group's identity remains unknown, a joint statement issued by the FBI, CISA, ODNI, and the NSA in early January said that it is likely a Russian-backed hacking group.
Microsoft also said in February that the SolarWinds hackers had downloaded source code for a limited number of Azure, Intune, and Exchange components.




