You can expect ransomware in America in the next few weeks which has a Breaking Bad theme. Take this a bit further and we can expect ransomware with Halloween themes later this year. Sheesh.
Some criminals are too smart for their own good though, because using a TV show like this will make it much more recognizable and written about, defeating the purpose.
Apart from the Breaking Bad theme, CryptoLocker.S. is pretty generic ransomware. It is surprising how fast ransom Trojans have developed. A year ago every new strain was headline news, now it's on page 3. This version grabs a wide range of data files, encrypts it using a random AES key which then is encrypted using a public key.
Your employees can run into this strain like any other ransom Trojan by opening an infected email attachment. It even opens a legitimate PDF file to trick your users that everything is fine. In the mean time, back at the server farm... Anyway, block all zip files at the edge if you have not already.
The crypto ransomware targets files with the following extensions for encryption:
- .ai
- .crt, .csv
- .db, .doc, .docm, .docx, .dotx
- .gif
- .jpeg, .jpg
- .lnk
- .mp3, .msi
- .ods, .one, .ost
- .p12, .pdf, .pem, .pps, .ppsx, .ppt, .pptx, .psd, .pst, .pub
- .rar, .raw, .rtf
- .tif, .txt
- .vsdx
- .wma
- .xls, .xlsm, .xlsx, .xml
- .zip
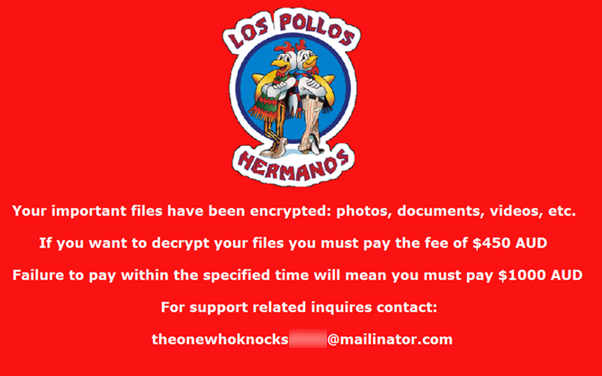
The malware authors cooked up their ransom demand message using the ‘Los Pollos Hermanos’ branding image found in the show. Along with this, part of the email address used in the extortion demand is based on a quote by the show’s protagonist Walter White, who declared "I am the one who knocks."
Details at Symantec who found it first:
http://www.symantec.com/connect/blogs/breaking-bad-themed-los-pollos-hermanos-crypto-ransomware-found-wild
Security Awareness Training for employees is a must these days. Find out how affordable this is for your organization and be pleasantly surprised.