 Webroot revealed the results of their 2019 Threat Report, showing that tried-and-true attack methods are still going strong, but new threats emerge daily, and cybercrime is highly innovative.
Webroot revealed the results of their 2019 Threat Report, showing that tried-and-true attack methods are still going strong, but new threats emerge daily, and cybercrime is highly innovative.
Hal Lonas, Webroot's CTO said: “We wax poetic about innovation in the cybersecurity field, but you only have to take one look at the stats in this year’s report to know that the true innovators are the cybercriminals. They continue to find new ways to combine attack methods or compromise new and existing vectors for maximum results. My call to businesses today is to be aware, assess your risk, create a layered approach that protects multiple threat vectors and, above all, train your users to be an asset—not a weak link—in your cybersecurity program.”
We could not agree more. Here are some highlights:
A whopping 40 percent of malicious URLs were found on good domains. Legitimate websites are frequently compromised to host malicious content. To protect users, cybersecurity solutions need URL-level visibility or, when unavailable, domain-level metrics, that accurately represent the dangers. Very often, endpoint security does not have these, or they run hours behind, which means these links wind up in your user's inbox.
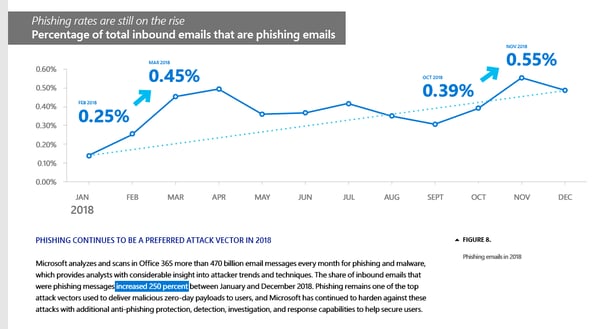
Phishing attacks increased 36 percent, with the number of phishing sites growing 220 percent over the course of 2018. Phishing sites now use SSL certificates and HTTPS to trick internet users into believing they are secure, legitimate pages.
Microsoft's latest Security Intelligence Report confirms this, they even show figures that phishing messages into Office 365 increased 250 percent over 2018.
Seventy-seven percent of phishing attacks impersonated financial institutions, and were much more likely to use HTTPS than other types of targets. In fact, for some of the targeted financial institutions, over 80 percent of the phishing pages used HTTPS. Google was found to be the most impersonated brand in phishing overall.
Webroot claims that after 12 months of security awareness training which combines phishing simulation campaigns with interactive, on demand training through the browser, end users are 70 percent less likely to fall for a phishing attempt. KnowBe4's numbers show closer to 90%.
Nearly a third of malware tries to install itself in %appdata% folders. Although malware can hide almost anywhere, Webroot found several common locations, including %appdata% (29.4 percent), %temp% (24.5 percent), and %cache% (17.5 percent), among others. These locations are prime for hiding malware because these paths are in every user directory with full user permissions to install there. These folders also are hidden by default on Windows® Vista and up.
Devices that use Windows 10 are at least twice as secure as those running Windows 7. Webroot has seen a relatively steady decline in malware on Windows 10 machines for both consumer and business. And then there's of course Windows Defender running on those machines, which is a very capable AV engine these days.
While ransomware was less of a problem in 2018, it became more targeted, and companies will still fall victim to ransomware. Many ransomware attacks in 2018 used the Remote Desktop Protocol (RDP) as an attack vector, leveraging tools such as Shodan to scan for systems with inadequate RDP settings. These unsecured RDP connections may be used to gain access to a given system and browse all its data as well as shared drives, providing criminals enough intel to decide whether to deploy ransomware or some other type of malware. Explore the Webroot report here.




