A massive survey of nearly 1,200 IT security practitioners and decision makers across 17 countries reveals that half the people who fell victim to ransomware infections last year were able to recover their files after paying the ransom demand.
The survey, carried out by research and marketing firm CyberEdge Group, reveals that paying the ransom demand, even if for desperate reasons, does not guarantee that victims will regain access to their files.
Timely backups are still the most efficient defense against possible ransomware infections, as it allows easy recovery.
Over a quarter of all victims lost their data for good
The survey reveals that 55% of all responders suffered a ransomware infection in 2017, compared to the previous year's study, when 61% experienced similar incidents.
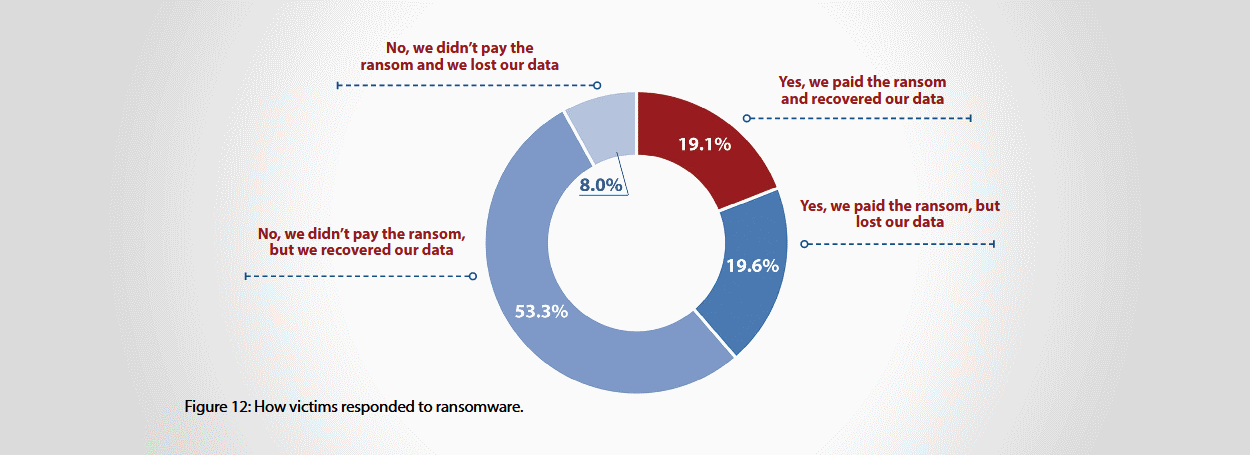
Of all the victims who suffered ransomware infections, CyberEdge discovered that 61.3% opted not to pay the ransom at all. Some lost files for good (8%), while the rest (53.3%) managed to recover files, either from backups or by using ransomware decrypter applications.
Of the 38.7% who opted to pay the ransom, a little less than half (19.1%) recovered their files using the tools provided by the ransomware authors.
The rest (19.6%) lost their data. Ransomware authors either didn't provide ransomware decryption instructions or apps, or these tools did not yield expected results.
Overall, the study found that over a quarter of ransomware victims (27.6%) lost their data for good, either by paying or not paying the ransom demand.
Lack Of Security Awareness A Tie With Lack Of Skilled Personnel
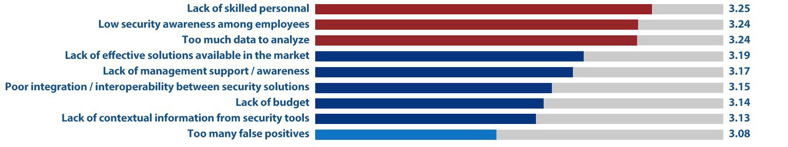
They wrote: "Each year, we ask respondents to tell us what’s inhibiting them from defending their respective organizations against cyberthreats. In other words, what’s standing in their way?
When we first asked the question in 2013 (for our 2014 CDR), we thought for sure that “lack of budget” would come out on top. We were shocked when it only came in at second place, right after “low security awareness among employees.” But what’s even more surprising is that “low security awareness among employees” remained the top concern among security professionals for the next three years – until this year (see Figure below.
In 2018, there is a new king of security inhibitors – “lack of skilled personnel.” But if you’ve been paying close attention to
inhibitor rankings over the last four years, this shouldn’t come as a surprise: 2014: fifth place; 2015: fourth place; 2016: third place; 2017: second place; 2018: first place.
This doesn’t mean that “low security awareness among employees” is no longer of concern. Far from it. In fact, it
was only nudged out of first position by one-hundredth of a point. Furthermore, you could say that there was a virtual three-way tie for first place, with “too much data to analyze” also one-hundredth of a point behind.
Stepping onto our proverbial soap box for a moment, we want to reiterate our shock and disappointment about IT
security organizations’ not doing enough to train company personnel about how to minimize cybersecurity risks through
safe computing. (Hello? Is anyone listening? Bueller? Bueller?)
Suffering from a shortage of high-quality security talent is completely understandable. But failing – year after year – to
invest in your company’s “human firewall” is both inexplicable and inexcusable. Okay, we’ve put away our soap box until
next year".
7 other findings of the CyberEdge survey:
- 77% of all organizations suffered a form of cyber-attack in 2017 (down from79% in 2016).
- Security-related budgets are prognosticated to rise in 2018 with 4.7% compared to last year.
- Security-related budgets are expected to account for 12% of the overall IT budget for companies in 2018.
- Four in five organizations said they are experiencing a shortage of personnel with IT security skills.
- Nine in ten companies are experiencing cloud-related security and privacy problems.
- Survey respondents said they perceive mobile devices and app containers (Docker, Kubernetes, Cloud Foundry) as their organization's weakest link in terms of security.
- Respondents said they plan to invest money in 2018 in advanced malware analysis/sandboxing (network security), containerization/micro-virtualization (endpoint and mobile security), and API gateway (application and data-centric security).
Free Ransomware Simulator Tool
How vulnerable is your network against a ransomware attack?
Bad guys are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
KnowBe4’s "RanSim" gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 10+ infection scenarios and show you if a workstation is vulnerable to infection.
Source: BleepingComputer





