 This latest attack demonstrates how cybercriminals can leverage one organization as merely a part of a larger phishing campaign to scam countless individuals out of credentials or money.
This latest attack demonstrates how cybercriminals can leverage one organization as merely a part of a larger phishing campaign to scam countless individuals out of credentials or money.
Once an attacker has admin access to your network, it’s really up to them what they want to do – it could be steal data, hold data for ransom, commit fraud, etc. Or, in the case of the Special Olympics of New York, leverage their email system to reach their approximately 67K registered families with an adult or child having an intellectual disability.
Their email server was apparently hacked in December and was used to send out phishing emails to their donors under the guise that a donation of nearly $2,000 was about to be posted automatically (creating the necessary sense of urgency on the part of the potential victim).
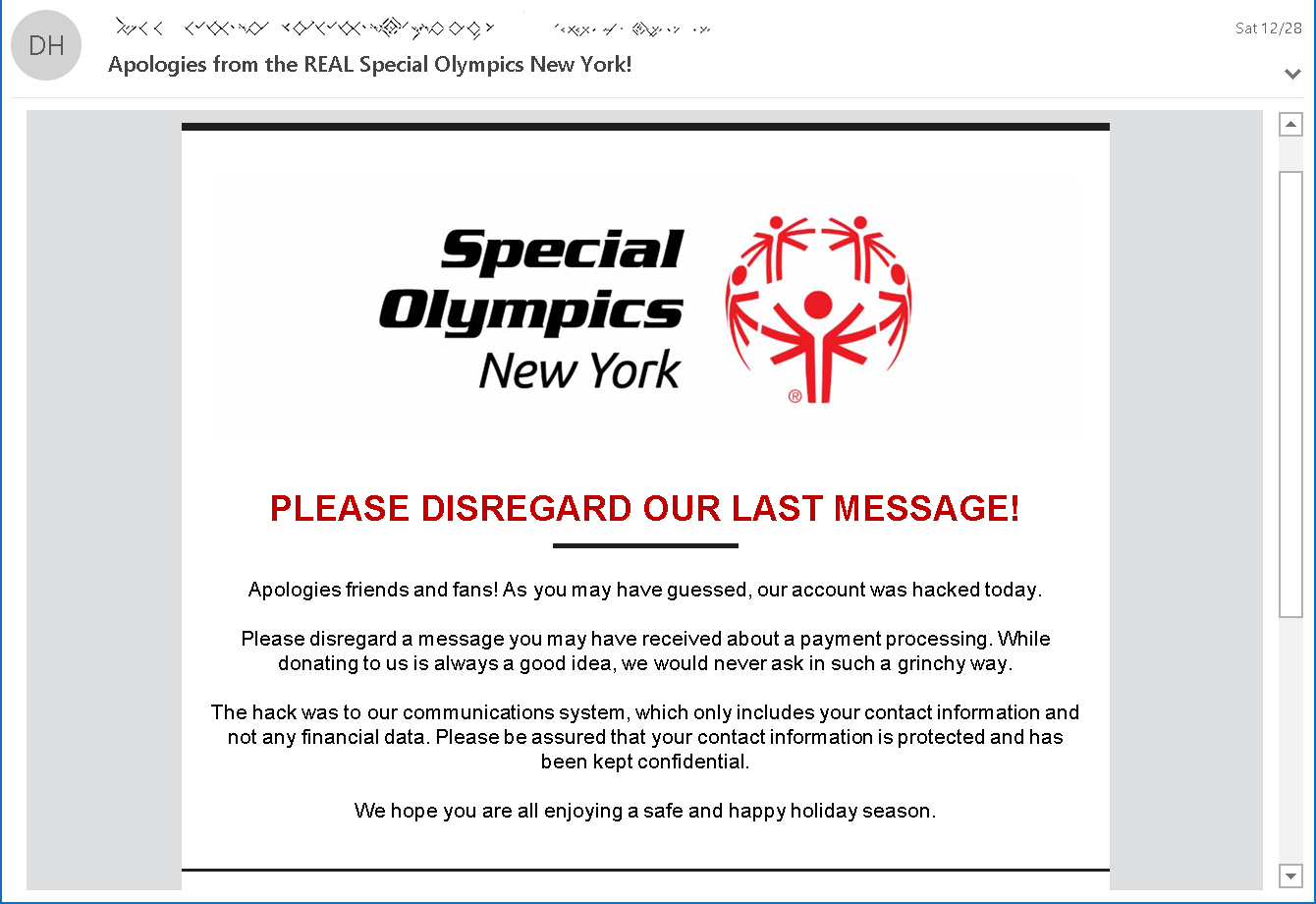
Upon realizing the email had been sent out, a follow-up email was sent, communicating that Special Olympics New York was aware of the hack, that donors should ignore the email, and that no information – other than contact details – was accessed.
This kind of attack fits the “Vendor Email Compromise” attack vector category, where the focus is purely to use email as a means of attack. In the case of the Special Olympics, it appears the focus was to steal credit card details from donors. But this kind of attack can just as easily be used to commit fraud, steal user credentials, install ransomware, or gain remote access to another network.
Organizations should be vigilant against any kind of potentially suspicious email that could be part of a phishing campaign. Users that undergo Security Awareness Training are already keenly aware of these kinds of attacks, know how to identify them before mistakenly engaging with them, and keep their employers safe from phishing attack.




