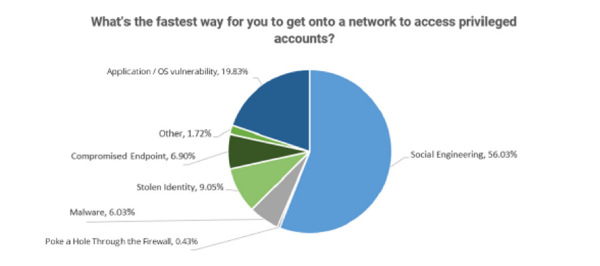
Despite the presence of application and OS vulnerabilities – both new and old – hackers prefer to leverage social engineering as their preferred attack method.
Every year at the Black Hat conference, Thycotic gathers data from the industry’s best hackers, seeking to understand exactly how they are getting in. With 60% identifying themselves as “White Hat” hackers, they were eager to share in this year’s Black Hat Survey Report.
The most astounding data point was that hackers aren’t interested in spending time to identify a vulnerability and develop an exploit; instead, over half of them (56%) find social engineering the fastest way to gain access to privileged accounts. This represents more than double those choosing to go the OS/Application vulnerability route.
According to the report, 85% of breaches involve compromised endpoints, pointing a finger at the need for users to be educated on social engineering scams, phishing attacks, and other modes of attack using Security Awareness Training to reduce the likelihood of becoming a victim.

We've got something really cool for you: the new Phishing Security Test v3.0!
Sending simulated phishing emails is a fun and an effective cybersecurity best practice to patch your last line of defense… your users.
Find out the Phish-prone percentage™ of your organization with our free updated Phishing Security Test that now includes our New Industry Benchmarking. See where you stack up! Industry Benchmarking enables you to compare your organization’s Phish-prone percentage with others in your industry.
Find out how you are doing compared to your peers and see the difference 12 months can make after using the integrated KnowBe4 Simulated Phishing and Security Awareness Training platform!
With Our Updated Phishing Security Test: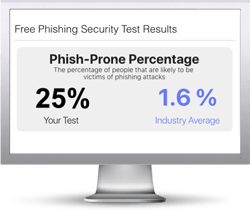
- You can customize the phishing test based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Start phishing your users now. Fill out the form, and get started immediately. There is no cost.
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:





