.jpg?width=300&name=iStock-1090872318%20(2).jpg) The latest string of attacks leverage traditional spear-phishing techniques mixed with the use of Microsoft’s newsletter service, Sway, to trick executives into giving up their Office 365 credentials.
The latest string of attacks leverage traditional spear-phishing techniques mixed with the use of Microsoft’s newsletter service, Sway, to trick executives into giving up their Office 365 credentials.
The group, dubbed perSwaysion for their use of Microsoft Sway as part of the attack, have successfully executed a string of campaigns aimed at stealing the Office 365 credentials of executives in over 150 companies.
The simple attack uses a non-malicious PDF attachment that links to a Microsoft Sway page that then links to a spoofed Office 365 logon page that collects the executive’s credentials. The success of such an attack puts organizations at risk; we’ve seen plenty of email account takeovers resulting in massive financial losses that the perSwaysion attack could facilitate.
According to security vendor Group-IB who spotted this new attack group, email is dumped via API and the email account owner's high-level business connections are established and documented. The attackers then perform a sort of island hopping, creating new PDFs that will be sent from the initially-compromised account to other high-ranking execs outside the organization with who they do business.
This kind of success highlights the need for even executives to undergo continual Security Awareness Training to be able to identify potentially malicious emails, as well as be subject to phishing testing to provide security teams with a feedback loop as to whether executives pose a risk to the organization.
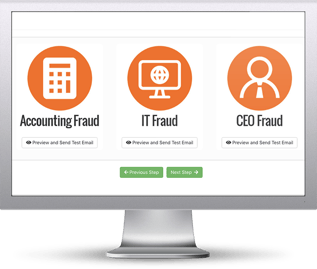 Here's how it works:
Here's how it works:




