 A few months ago, KnowBe4 began offering customers two new kinds of scientifically-based assessments to help IT departments get a better handle on the internal security culture within their organizations and identify weaknesses in security knowledge amongst their employees. Both types of assessments -- the Security Awareness Proficiency Assessment (SAPA) and Security Culture Survey (SCS) -- are designed to assist customers who are rolling out KnowBe4's Security Awareness Training to their employees.
A few months ago, KnowBe4 began offering customers two new kinds of scientifically-based assessments to help IT departments get a better handle on the internal security culture within their organizations and identify weaknesses in security knowledge amongst their employees. Both types of assessments -- the Security Awareness Proficiency Assessment (SAPA) and Security Culture Survey (SCS) -- are designed to assist customers who are rolling out KnowBe4's Security Awareness Training to their employees.
These survey-driven assessments are fairly simple to use. Send out emails like this to your employees...
...and we'll return some very useful data about your users, where they stand on their journeys to becoming "woke" to security threats, and point out who needs help and where.
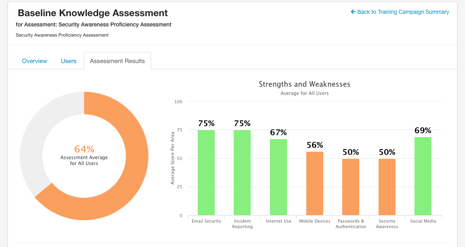
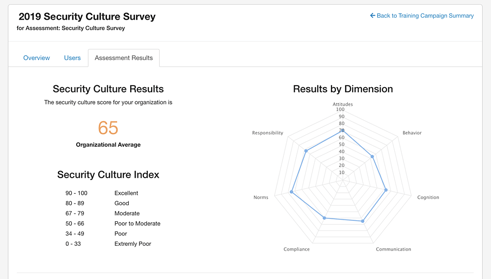
If you're serious about doing Security Awareness Training right, this is the kind of data you need.
Imagine our curiosity, then, when we discovered that someone else has apparently decided to jump into the security training survey game by pushing their own surveys into users inboxes. Who could it be?
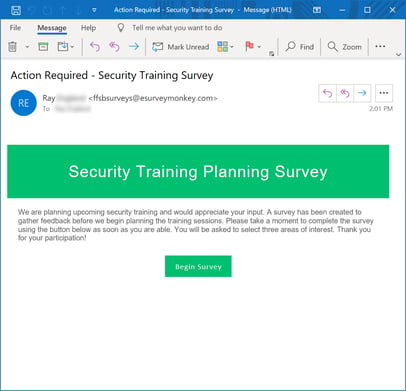
Have you figured it out? Wanna take a wild guess? Still need a few clues? Maybe the landing page for this "Security Training Planning Survey" will help.
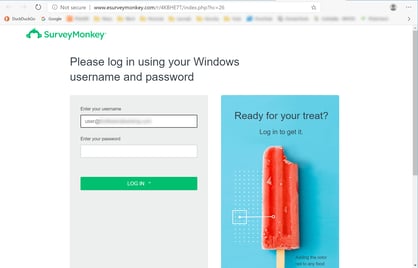
Yeah, it's THEM. But didn't you already sort of know it was going to be the "usual suspects"?
For those who are still a bit mystified, the above is a phish -- a straight-up credentials phish, in fact. And it's rather nicely executed, if we do say so ourselves. (The red lollipop is certainly a cute touch.)
The initial email is simple, clean, and straightforward -- no obvious typos or mechanical errors, and the language seamlessly slips into that familiar, simple, yet slightly vacuous prose style so common to Western business communication. Better yet, there's a Big Green Button just in case anyone gets confused as to just what's being asked of them. And the survey, as it were, is hosted on a rather slickly designed spoof of SurveyMonkey's well-known web site.
After users finish coughing up their login credentials, they get shuffled along to an actual survey page -- of sorts.
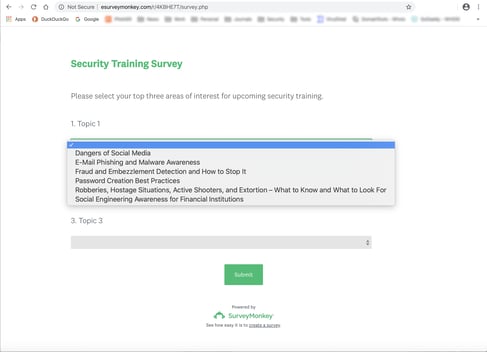
The curious thing about this "security training planning survey," though, is that the most important question being answered here isn't any of the ones being explicitly asked. And that question is: which of your users is gullible enough to hand over their account to malicious actors?
The bad guys are eager to know! (As are you, for that matter.) Unfortunately, we're guessing the bad guys behind this survey won't be sharing any of their data.
Our official response to this "Security Training Planning Survey" (beyond being mildly flattered) is a simple one:

Actually, this "survey" shouldn't come as a surprise. The bad guys are in fact very close observers of trends within the business world, and they've picked up on the fact that organizations like yours are now regularly sending out surveys to employees.
Rather predictably, the bad guys have decided they like sending out surveys, too: employee engagement/satisfaction surveys, workplace culture surveys, health care benefits surveys, holiday activity surveys, and now, of course, security training surveys. They'll even do employee performance assessments for you, if you let them. (Sorry, they're not sharing data from those either.)
We're still waiting for the fake security awareness training courses, which are surely coming. (Those should be a hoot.)
The proper response to all of this, of course, is to step your users through actual Security Awareness Training proven to get your users up to speed on the latest threats landing in their inboxes -- real training driven by real data from scientifically-based assessments of the security culture (or lack thereof) within your organization and your users' proficiency in identifying and handling the kinds of security threats they are facing day in and day out.
Put simply, if you want to know just who in your organization is gullible enough to hand over their credentials to malicious actors -- or bring down your entire network with a ransomware infestation, for that matter -- better to let us tell you before the bad guys hit your users with one of their "surveys" and figure it out before you do.
