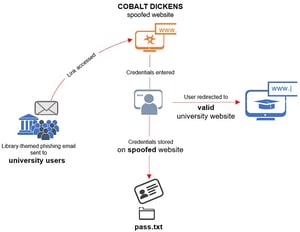
 Researchers at Secureworks’ Counter Threat Unit (CTU) have been tracking a major phishing campaign that’s using library-themed emails to target more than sixty universities around the world. Secureworks attributes the campaign to “Cobalt Dickens,” a threat group associated with the Iranian government.
Researchers at Secureworks’ Counter Threat Unit (CTU) have been tracking a major phishing campaign that’s using library-themed emails to target more than sixty universities around the world. Secureworks attributes the campaign to “Cobalt Dickens,” a threat group associated with the Iranian government.Most people assume they aren’t important enough to be targeted by state-sponsored hackers, but universities, companies, and of all types and sizes can be targeted by advanced attacks. Universities offer access to valuable intellectual property, financial information, and personal data that can be used in further attacks.
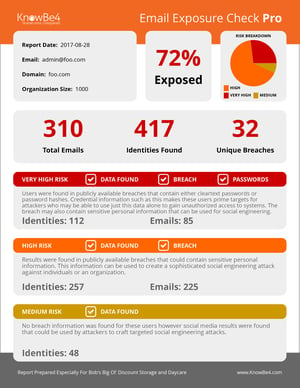
Secureworks recommends that all universities implement multi-factor authentication to combat these threats, stating that the risk of using passwords alone outweighs the inconvenience of an extra step for security. New-school security awareness training can help people realize the importance of using multi-factor authentication, as well as teaching them how to recognize phishing attacks.
Secureworks has the story: https://www.secureworks.com/blog/cobalt-dickens-goes-back-to-school-again
 Here's how it works:
Here's how it works:




