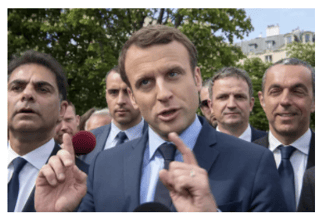
 The French presidential election has been hit with a case of déjà vu. Emmanuel Macron's campaign said its staff received phishing emails meant to steal their passwords.
The French presidential election has been hit with a case of déjà vu. Emmanuel Macron's campaign said its staff received phishing emails meant to steal their passwords.
Trend Micro said in a report set to be published today that they have found evidence of a phishing attack targeting French presidential candidate Emmanuel Macron. The emails and fake sites sites could have tricked campaign staff into entering their credentials and allow malware to infect their computers, their researchers stated.
Macron, of the relatively new "En Marche" party which translates to "on the move", will be in a runoff on May 7 against National Front candidate Marine Le Pen for the French presidency. Macron's campaign confirmed to the Wall Street Journal that its staffers received emails leading to fraudulent websites, but that the attempts were blocked, but who knows if they really were.
The hacking group behind the phishing attempts was Russian APT28, a group tracked for years by many security researchers. This group of criminal hackers is also known as Pawn Storm, Sofacy, Strontium, Fancy Bear, and SecureWorks calls them "IRON TWILIGHT". Here is a backgrounder on APT28.
As part of the attack, hackers set up multiple internet addresses that mimicked those of the campaign’s own servers in an attempt to lure Mr. Macron’s staffers into turning over their network passwords, said Feike Hacquebord, a senior threat researcher for Tokyo-based Trend Micro and the author of the report, a copy of which was reviewed by The Wall Street Journal.
Security researchers state it is highly likely APT28 are supported by the Russian Government, specifically the GRU which is the Russian military intelligence arm, the counterpart of the FSB (former KGB). APT28 "active measures" were trying to influence U.S. presidential elections and at the moment try to do the same thing in France and Germany. Kremlin spokespeople deny everything vehemently. Yeah, sure.
What to do about It
SecureWorks recommends the following excellent best practices to prevent network compromise:
- Apply best-practice security controls such as regular vulnerability scanning and patching,
- Have network monitoring tools in place.
- User education reduces your susceptibility to compromise.
- Implement two-factor authentication (2FA) on internal and third-party webmail platforms.
- Encourage employees use 2FA on their personal accounts.
- Restrict work-related communication from personal email.
If you want to spend less time putting out fires, get more time to be proactive, and get the things done you know need to be done, step your employees through effective security awareness training. It will help you prevent compromises like this or at least make it much harder for the bad guys to social engineer your users. More than 9,000 of your peers are using KnowBe4. Find out how affordable this is for your organization. Get a quote now:
Don't like to click on redirected buttons? Copy & Paste this link in your browser:





