 Should you find yourself in the situation where paying the ransom is your only out, it’s important to know how to navigate – and minimize – the payment.
Should you find yourself in the situation where paying the ransom is your only out, it’s important to know how to navigate – and minimize – the payment.
Cyber attacks are the new reality for most organizations. According to a new report from Cyber Edge, over 87% of organizations think a cyber attack is likely in 2018, and 77% have experience one or more attacks in the previous 12 months. Ransomware ranks #2 in Cyber Edge’s list of cyberthreat concerns (just behind malware) and is predicted to reach $8 billion in damages (according to Cybersecurity Ventures) in 2018 alone.
With ransomware, there’s always the question of “Should I pay the ransom?”
Most experts in cyber security, including the FBI and the UK’s National Crime Agency agree that paying the ransom should be a last resort. You’re funding criminals that aren’t guaranteeing that your data will be properly encrypted. Additionally, it potentially encourages further attempts at extorting funds from your organization.
BUT… if you’re in the situation where you’re only option is to pay the ransom, how do you minimize the cost?
- Talk to the hackers – If possible, begin communications as soon as possible. Sometimes tactics like claiming no ability to pay, etc. can have an impact. One story about last year’s WannaCry had an unexpected ending, with the hackers providing great customer service to a region of the world with no means to pay a ransom.
- Ensure Decryption is Possible – According to the Cyber Edge report, of those organizations paying the ransom, only half got their data back. Asking the hacker to prove they can properly decrypt is probably a must.
- Haggle – remember, the hackers are in business to make money. They’d rather make something than nothing. You should expect pushback on your first few attempts, but by a third communication, hackers tend to consider decreasing the fee.
Even if you’re successful, keep in mind there may be other ramifications – compliance penalties, damage to corporate reputation, etc.
Rather than be stuck in this situation, there are some proactive steps you can take to avoid a ransomware attack:
- Backup Everything Important – treat a ransomware attack like a disaster scenario in your DR planning. Determine which data sets and systems are mission critical, ensuring you have an ability to recover them easily.
- Educate Your Users – organizations that employ Security Awareness Training experienced 37% less ransomware attacks than those using multiple mainstream security solutions.
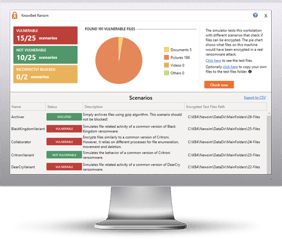
Bad guys are constantly coming out with new malware versions to evade detection. That’s why we’ve updated our Ransomware Simulated tool “RanSim” to include a new cryptomining scenario!
This new cryptomining scenario simulates a Monero cryptocurrency-mining operation on the local machine. Monero mining is the most popular cryptocurrency mined by real-world malware and takes a lot of CPU and GPU cycles to process the data necessary to generate the currencies.
Try KnowBe4’s NEW Ransomware Simulator tool and get a quick look at the effectiveness of your existing network protection against the latest threats.
RanSim will simulate 13 ransomware infection scenarios and 1 cryptomining infection scenario to show you if a workstation is vulnerable to infection.
Here's how RanSim works:
- 100% harmless simulation of real ransomware and cryptomining infection scenarios
- Does not use any of your own files
- Tests 14 different types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
This is a complementary tool and will take you 5 minutes max. RanSim may give you some insights about your endpoint security you never expected!
Download the new Ransim here:
https://info.knowbe4.com/ransomware-simulator-tool-1