Social Engineering tactics seek to use any means that’s familiar to the intended victim – and unsubscribing is perceived as being so benign, it may just be the perfect way to fool your users.
While I can’t think of a single website I’ve visited in the last year that sends me an email after I’ve unsubscribed to confirm my decision, I must admit, this method of usurping the user’s sense of suspicion is pretty good.
Nobody wants to continue receiving unwanted emails. And most of us have received emails from companies we’ve never heard of. And so, we unsubscribe using the link at the bottom of said emails. Imagine, then, a user’s delight to receive an email allowing them to unsubscribe proactively from something they neither recognize nor want.
What’s genius about this is it leverages our constant bombardment with emails from businesses we don’t know (which means these scammers don’t need to necessarily appear to be a business we are engaged with). Its message is also one that creates a positive association between the user and the email – one that will get more users to click the malicious link.
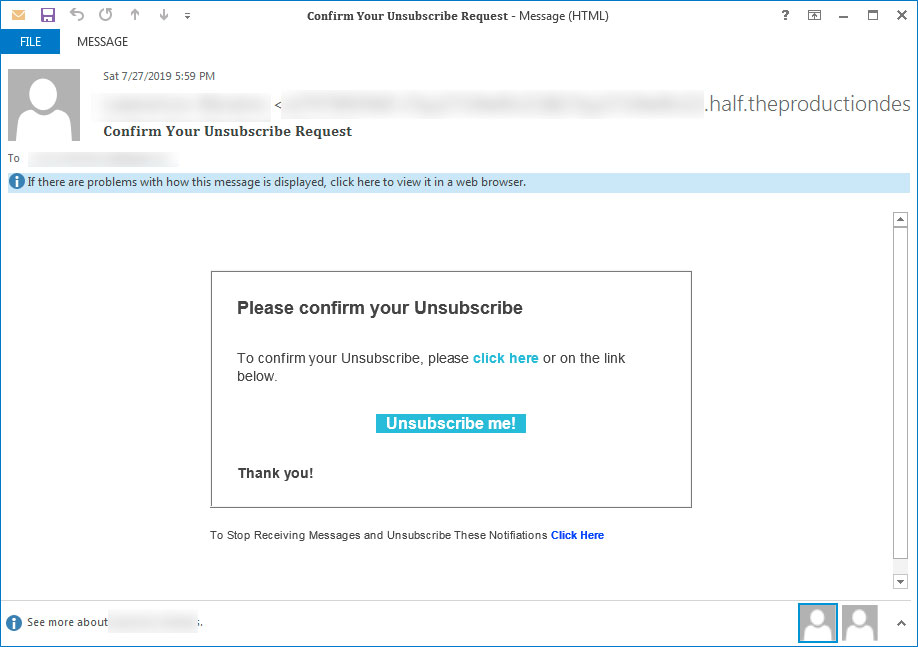
In the case of the example above, clicking the unsubscribe email only sends an “unsubscribe” email to a set of what are assumed to be scammer email addresses so they are aware your email address is a live account. But it’s just as feasible to use the link to download malware, or take the user to a site laden with malicious code.
Users need to be wary of any emails that are unfamiliar to them. It’s better to mark them as spam or junk than it is to engage with the email in any form. These kinds of best practice responses can be taught using continual Security Awareness Training, as well as how to spot suspicious email content.
 Here's how it works:
Here's how it works:




