 Unlike the traditional methods of notifying victim organizations by simply taking over a computer or providing a “readme” text file, this new method has some devilish benefits.
Unlike the traditional methods of notifying victim organizations by simply taking over a computer or providing a “readme” text file, this new method has some devilish benefits.
Ransomware follows a pretty simple attack strategy:
- Step 1: Encrypt everything you can
- Step 2: Notify the victim
- Step 3: Collect the ransom
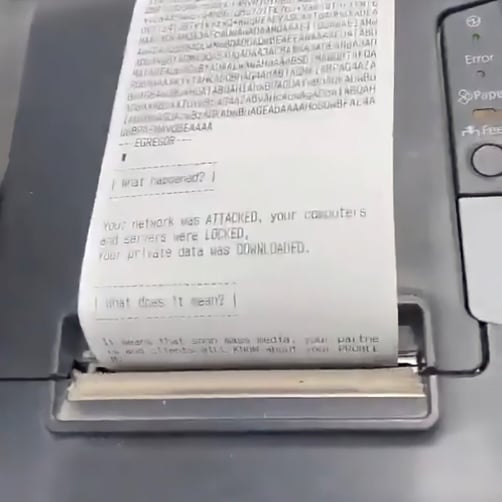
But following in the footsteps of ransomware authors like Maze who has chosen to go a step further to make their attacks more impactful, the Egregor ransomware has gone where no other has gone before: paper.
Egregor victims have experienced print jobs being sent to every available printer that notify the reader that all computers and servers are locked, data has been stolen, and “next steps” to take to rectify the situation.
Source: Twitter
What makes this so brilliant is that most organizations want to keep successful ransomware attacks under wraps, minimizing the possibility it becomes public and impacts customer trust, stock prices, revenue, etc.
But in the case of Egregor, the goal is to maximize the number of people who are notified, making it common knowledge that an attack has occurred – take the image above as a perfect example: that’s a receipt printer!!!
The bad guys are getting MUCH better at this – I fear faster than the good guys are evolving their protective measures. So, it’s up to the organization itself to stop these attacks. Analysis of the ransomware suggests that phishing attacks are the primary attack vector, putting your users dead center in the attack, determining whether it succeeds or fails based on whether they click the malicious link or attachment.
Security Awareness Training is a key element in stopping all forms of ransomware that use phishing scams to gain entry. By teaching them how to spot scams before engaging with them, users can act as a part of your security strategy, strengthening the organization’s position and shrinking the attack surface.
 Here's how it works:
Here's how it works:




