Antivirus companies are not going to like this. Microsoft blogged that their Windows Defender Advanced Threat Protection (ATP) security service soon will be coming to Win7 and Win8.1 clients.
The service will be available at the public preview stage this spring. It'll be available more broadly starting sometime "this summer," which likely means it'll go into production by then.
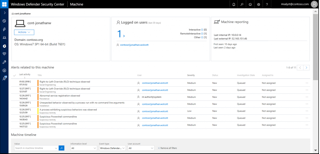
Windows Defender ATP is a post-breach detection service originally associated with Windows 10 clients, which was unveiled almost two years ago. It uses machine learning and Microsoft security expertise to detect threats in computing environments.
Microsoft later indicated it was adding autoremediation capabilities to this service through its integration of Hexadite technology, so the service is also designed to automatically fix security problems.
Late last year, Microsoft suggested that Windows Defender ATP could protect Windows Server 2012 R2 and Windows Server 2016 machines, too, and its security was also extended to Linux devices, including Android, iOS and macOS machines... Continue reading at RedmondMag
In other related news.. Drivers are a glaring attack target
Microsoft has released an updated guide on driver security. This new guide offers advice that developers could use to ensure Windows drivers are secured against basic attacks and preventable flaws.
The new guide —also available as a one-document PDF— is authored by Microsoft's Don Marshall and comes to replace an older help page and includes:
→ A guide on driver threat modeling
→ A guide on how drivers should integrate into the overall Windows security model
→ A tutorial on how to use the Device Guard Readiness Tool to evaluate a driver's Hypervisor-protected Code Integrity (HVCI) compatibility
While the driver security checklist is a must-read for any software developer and not just driver authors, the guide on assessing "threat modeling for drivers" is also something that software engineers should take a peek at.In particular, threat modeling refers to the process of identifying the points at which a driver could be vulnerable to an attack, what types of attacks could be mounted at each point, and what driver designs are available to thwart each attack.
Combining the knowledge shared in these first two documents will help driver developers understand basic principles of driver security design they could apply on any OS.




