Security researchers at Check Point have discovered yet another attack that leverages legitimate web applications to host attacks in order to bypass security scanners.
Security researchers at Check Point have discovered yet another attack that leverages legitimate web applications to host attacks in order to bypass security scanners.
One of the easiest ways for a security solution to spot a phishing attack is to evaluate the webpage a malicious link takes the recipient to. However, we’ve seen plenty of examples where legitimate websites were misused to present malicious content – as is the case of a new attack identified by Check Point in which Google Looker Studio is used.
Google Looker Studio is a tool that converts slideshows, spreadsheets, and other data sources into visualized data, such as charts and graphs.
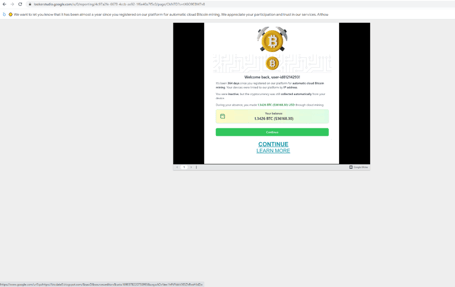
But according to Check Point, cybercriminals have figured out ways to leverage the site. Instead of presenting malicious content (such as the Google Slideshow below) the webpage was designed to look like a Bitcoin mining site that eventually leads to a malicious website intent on stealing credentials:
Source: Checkpoint
While the uncovered attack above doesn’t impact organizations in particular, it’s the use of legit websites like Google Looker Studio that present a problem to security solutions. The Google Slideshow in question provides enough obfuscation prior to placing the victim on a malicious webpage that security solutions won’t detect it as malicious.
Shift the attack theme to something business-related and make the pages look like Microsoft 365 and NOW you begin to see where this is a problem for organizations – and it’s the reason why organizations need to implement continual security awareness training to educate users on such tactics to avoid being the next victim.