.jpg?width=369&name=iStock-1213223956%20(2).jpg) From Services, to Distribution, to Monetization, cybercriminals are getting so organized, cybersecurity experts are now beginning to see how vast the relationships and connections really are.
From Services, to Distribution, to Monetization, cybercriminals are getting so organized, cybersecurity experts are now beginning to see how vast the relationships and connections really are.
It’s worrisome when your organization comes under cyberattack in the first place. But how about when you are under attack by an organized campaign that uses the best-in-breed dark infrastructure, phishing kits, social engineering, exploit kits, ransomware, and crypto services, and money laundering in the world?
That’s exactly the picture being painted in cybersecurity vendor CrowdStrike’s 2021 Global Threat Report. In this report, CrowdStrike has mapped out the observed relationships between known cybercriminal groups:
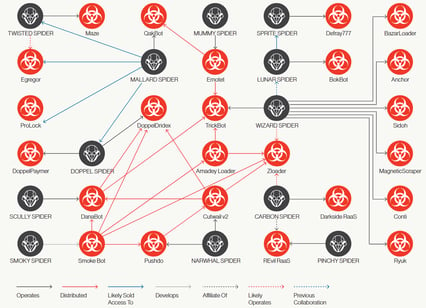
Source: CrowdStrike
CrowdStrike has also visualized all the cybercriminal services available today as an ecosystem. Be sure to read through each part of the image below – the implications are staggering!
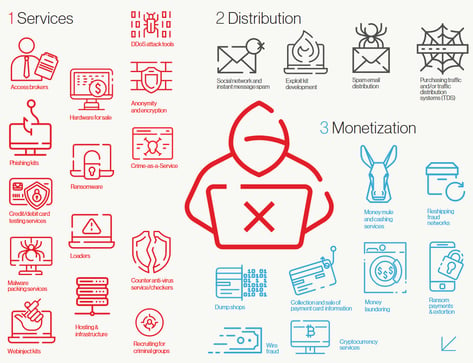
Source: CrowdStrike
The good news is that the majority of attacks today still require the intervention of a human user; whether it’s engaging with malicious email or web content, the bad guys need one of your users to participate in an attack by falling for social engineering tactics. This is good news because your organization can easily thwart these attacks by enrolling users in new school Security Awareness Training that teaches users how to put on a mindset of vigilance and to easily identify and avoid suspicious email messages and websites.




