 A mysterious update in the behavior of the CTB-Locker ransomware strain alerted security researchers to pull some strings and see what was going on.
A mysterious update in the behavior of the CTB-Locker ransomware strain alerted security researchers to pull some strings and see what was going on.
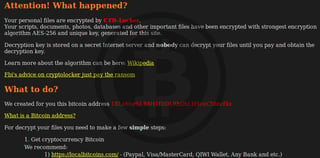
The CTB-Locker ransomware family, which is mainly known for infecting and locking individual machines, recently switched to targeting websites via a PHP version, first observed last February.
The change that caught the eye of Sucuri experts is an update to its "Free decrypt" page where users could unlock one free file per infection. It didn't take long for researchers to observe that the ransomware was using blockchain to deliver decryption keys for their victims using a special field in the Bitcoin transaction operation called OP_RETURN.
The Sucuri guys said: "So, instead of using unreliable gates on third-party hacked sites, the March version of the CTB-Locker reads the keys directly from public and much more reliable blockchain information services. That’s the beauty of Bitcoin transactions – everything is public and transparent, and at the same time it’s possible to keep things anonymous and not traceable to real IPs."
How it works: For each infected website, the cyber criminals were automatically creating a Bitcoin address, which they would monitor. If 0.0001 Bitcoin -- the minimum transaction fee-- was sent they would know it was for a free decrypt operation.
From another account, they would then initiate a fake transaction to the infected website's unique Bitcoin address. While this transaction never went through, it would be enough to get recorded in the blockchain as a failed operation, along with its OP_RETURN metadata.
Crooks would then use the Blockexplorer.com API to look at the OP_RETURN field which would hold the decryption key for the file submitted via the free decrypt operation. If the infected user paid the entire ransom, this same field would hold the entire master decryption key for all files.
The authors made the switch bcause payment gates were previosly hosted on infected websites and didn't make for a reliable method of payment tracking.
Looks like the criminals weren't very successful, in tracking the Bitcoin wallets no victims paid the full ransom and likely restored their websites via backups. More at the SucuriNet blog.
What To Do About Ransomware
Get the most informative and complete hostage rescue manual on Ransomware. This 20-page manual (PDF) is packed with actionable info that you need to prevent infections, and what to do when you are hit with malware like this. You also get a Ransomware Attack Response Checklist and Prevention Checklist.
Hat Tip to SoftPedia





