Lawrence Abrams from the famous bleepingcomputer site wrote at Spiceworks:
"CryptoWall 4.0 has been released that displays a redesigned ransom note, new filenames, and now encrypts a file's name along with its data. We were alerted to this new variant by various members who have posted about being infected by what was being called the help_your_files ransomware. Once we were able to analyze a sample, though, it was quickly determined that this was in fact a new version of CryptoWall." This is a screenshot from their site that shows what it looks like:
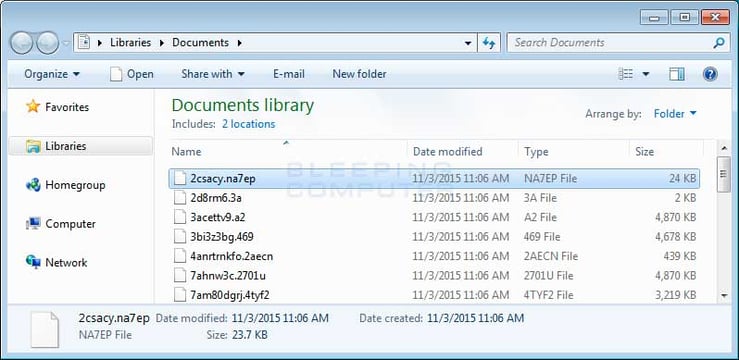
In summary, the new v4.0 release now encrypts file names to make it more difficult to determine important files, and has a new HTML ransom note that is even more arrogant than the last one.
Just a couple of examples from the new ransom note:
Cannot you find the files you need?
Is the content of the files that you have watched not readable?
It is normal because the files' names, as well as the data in your files have been encrypted.
Congratulations!!!
You have become a part of large community CryptoWall.
The new version is still using phishing emails as an infection vector, usually containing a 'resume' thet looks like a Word doc but is really a malicious JavaScript file.
Bleeping computer continued: "From analysis done by Nathan Scott, CryptoWall 4.0 has the same installation characteristics and communication methods as previous versions. When communicating with the Command & Control Servers, CryptoWall 4.0 continues to use RC4 encryption It also continues to create a victim's unique identifier from the MD5 hash of the computer's computer name, volume serial number, processor information, and OS version. Like its predecessors, when installed CryptoWall 4.0 will inject itself into Explorer.exe and disable System Restore, delete all Shadow Volume Copies, and use bcdedit to turn off Windows Startup Repair. It will then inject itself into svchost.exe and encrypt the data on all local drives, removable drives, and mapped network drives. Once it has completed encrypting your files it will launch the ransom notes that explain what happened and how to purchase the decrypter." Here is the full post at BleepingComputer.
Andra Zaharia of Denmark-based Heimdal Security says Cryptowall 4.0 is employing "vastly improved" communications and better code, so it can exloit more vulnerabilities. "Cryptowall 4.0 still includes advanced malware dropper mechanisms to avoid antivirus detection, but this new version possesses vastly improved communication capabilities," Zaharia says. "It includes a modified protocol that enables it to avoid being detected, even by second generation enterprise firewall solutions. "This lowers detection rates significantly compared to the already successful Cryptowall 3.0 attacks."
System administrators agree that one of the critical pieces of the puzzle to prevent ransomware infections is security awareness training combined with frequent simulated phishing attacks. Find out how affordable this is for your organization and be pleasantly surprised.