 A security alert from the FBI warns that hackers are launching credential-stuffing attacks against organizations in the financial sector, ZDNet reports.
A security alert from the FBI warns that hackers are launching credential-stuffing attacks against organizations in the financial sector, ZDNet reports.
“Since 2017, the FBI has received numerous reports on credential stuffing attacks against US financial institutions, collectively detailing nearly 50,000 account compromises,” the alert said. “The victims included banks, financial services providers, insurance companies, and investment firms.”
The Bureau explains that these attacks take advantage of the fact that many people reuse passwords or slight variations of passwords for multiple online accounts.
“When customers and employees use the same email and password combinations across multiple online accounts, cyber criminals can exploit the opportunity to use stolen credentials to attempt logins across various sites,” the FBI says. “According to a 2020 survey conducted by a data analytics firm, nearly 60 percent of respondents reported using one or more passwords across multiple accounts. When the attackers successfully compromise accounts, they monetize their access by abusing credit card or loyalty programs, committing identity fraud, or submitting fraudulent transactions such as transfers and bill payments.”
The alert describes some specific attacks involving credential stuffing, including one last year in which criminals compromised over 4,000 banking accounts.
“Between June and November 2019, a small group of cyber criminals targeted a financial services institution and three of its clients, resulting in the compromise of more than 4,000 online banking accounts, according to a credible financial source,” the Bureau says. “The cyber criminals then used bill payment services to submit fraudulent payments—about $40,000 in total—to themselves, which they then wired to foreign banking accounts. According to a 2020 case study on one of the firms, security researchers identified more than 1,500 email addresses and 6,000 passwords exposed in more than 80 data breaches. Some of the credentials belonged to company leadership, system administrators, and other employees with privileged access.”
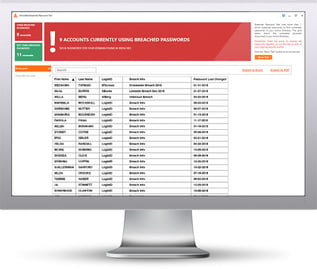
The FBI recommends that organizations implement a combination of technical solutions, policies, and education to combat credential stuffing attacks. For users, enabling multi-factor authentication and using unique passwords (preferably via a password manager) are two of the best steps they can take to protect their accounts. New-school security awareness training can help your employees avoid falling victim to these attacks.
ZDNet has the story.
 Here's how it works:
Here's how it works:




