 The latest iteration in Copyright Claim scams is an evolution of this repeated attack method that has proven to get the attention – and response – of victims over the last few years.
The latest iteration in Copyright Claim scams is an evolution of this repeated attack method that has proven to get the attention – and response – of victims over the last few years.
The scam itself is nothing new; I’ve covered it here when it was targeting Instagram credentials, and before that attempting to install the IceID information-stealing trojan. But according to security researchers at South Korean security vendor AhnLab, it’s LockBit ransomware’s turn.
The attack begins with (according to AhnLabs) a very similarly-written email about the recipient being in violation of a copyright held by the sender, informing the recipient to look at the attachment for more details on the violation.
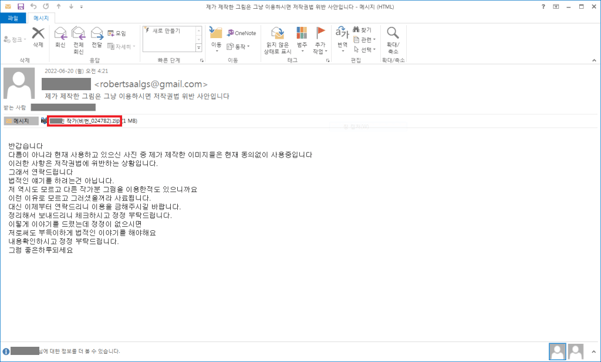
Source: Ahn Labs
The attack does make several attempts to obfuscate its’ malicious nature from security solutions by attaching a zip file that contains another compressed file – an executable disguised as a PDF document – that is actually an NSIS script file (Nullsoft Scriptable Install System) which is an open-source Windows installer.
There was no detail included around the industry, size, or geography of the campaign’s targets, but according to Palo Alto’s Unit42, LockBit 2.0 historically targets professional services, construction, wholesale and retail, and manufacturing companies.
And while AhnLab’s examples are in Korean, Unit42 notes that LockBit 2.0 has primarily targets the United States, Italy, Germany, Canada, France, the U.K., Spain, Thailand, Brazil and Switzerland.
Users within your organization – particularly those either in Marketing or Legal (who would actually care about a copyright claim) should be put through Security Awareness Training so they are aware of such scams, reducing the likelihood of the attack succeeding.
 Here's how it works:
Here's how it works:




