 This latest “new kid on the block” is gaining momentum and – according to CheckPoint – seeing successes with their attacks globally, calling their organizational structure “impressive.”
This latest “new kid on the block” is gaining momentum and – according to CheckPoint – seeing successes with their attacks globally, calling their organizational structure “impressive.”
It’s not often a ransomware gang gets a nod from a security vendor, but in this case, it appears to be warranted. In a recent article focusing on the ransomware gang Black Basta, the security analysts at the Check Point Incident Response Team showcase some details about this newest addition to the long list of ransomware families we’ve encountered.
According to CheckPoint, Black Basta has successfully attacked, exfiltrated data from, and leaked data belonging to 89 high-profile organizations since May of this year. Despite nearly half (44%) of the victim organizations residing in the U.S., Black Basta has been successful in their attacks globally:
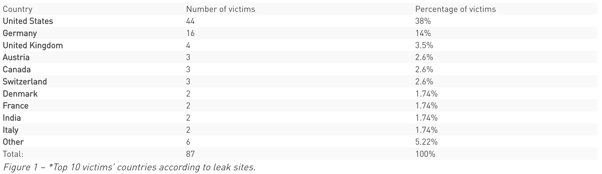
Source: Checkpoint
Do keep in mind, that the list above doesn’t include those organizations that paid the ransom to avoid leaked data being published.
According to CheckPoint, Black Basta uses a combination of malicious Office documents, QakBot, CobaltStrike Beacon, and their own ransomware payload as part of their attacks.
To avoid becoming a victim of a ransomware attack, CheckPoint recommend maintaining viable backups, keeping systems updates, scanning for malicious email content, monitoring file activity, and Security Awareness Training as effective ways to prevent and mitigate attacks.
 Here's how it works:
Here's how it works:




