 A recent Class-Action lawsuit against EHR vendor Allscripts raises the question of where fault should lie when ransomware attacks are successful.
A recent Class-Action lawsuit against EHR vendor Allscripts raises the question of where fault should lie when ransomware attacks are successful.
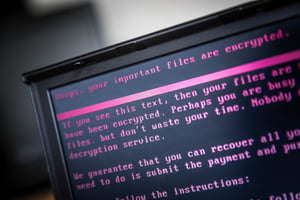
It’s every cloud providers nightmare: In January of this year, Allscripts was materially impacted by the SamSam variant of ransomware, causing over 1,500 doctor’s offices to be unable to access patient records. Over $300K was paid in ransom and Allscripts still took over a week to completely recover from the attack.
Surfside Non-Surgical Orthopedics in Boynton Beach, Fla., filed a class-action lawsuit against Allscripts claiming they failed “to secure its systems and data from cyberattacks, including ransomware attacks," the complaint reads. The lawsuit further alleges Allscripts' EHR and electronic prescription system outages resulted in canceled appointments, "significant business interruption and disruption, and lost revenues." Allscripts is asking that the lawsuit be dismissed.
Regardless of the outcome of the lawsuit, the story begs the question, can an organization ever truly stop ransomware?
In the lawsuit text above, you can see the plaintiff claiming Allscripts didn’t do enough to ensure the security of its data, applications, and systems. But, in their defense, cybercriminal organizations behind ransomware attacks have a few advantages that ensure there’s no way 100% of organizations are impenetrable:
- They avoid detection – even with AV, endpoint protection, email scanners, etc., malware today uses evasive techniques to keep from being detected by even the most cutting edge solutions.
- They test – ransomware developers have the ability to test their infection methods in isolated virtual environments with leading security solutions installed. This means they get to keep trying and improving their malware until it successfully infects while the good guys sit and wait until the malware is seen in the wild.
- The have an inside accomplice – well, sort of. Phishing attacks are one of the most viable ways to launch an attack, and your users are the accomplice. With story after story (even just on our blog!) of the numerous creative ways cybercriminals use to solicit clicks or obtain credentials, users become unwitting participants in most attacks.
So, what should you be doing to stop ransomware?
You should have a layered defense in place – it’s necessary to have an automated vigilant security infrastructure running 24/7. But, then there’s zero-day ransomware – the newest forms of ransomware that no defense has ever seen (except the one the attackers tested against). It’s likely that regardless of the solution-based defense you have, you won’t be able to stop a well-written, truly-new form of ransomware. That’s where your users come into play – by leveraging Security Awareness Training, users can be taught to incorporate a security-centric focus into their work. Interaction with email and the web is accomplished a scrutinizing eye.
We won’t know if Allscripts was truly prepared for the attack in January, but you can be certain that it’s possible to be prepared using a layered defense that includes Security Awareness Training.




