 According to Microsoft's Security Intelligence team, a recent business email compromise attack (BEC) has shown that threat actors are quickening the pace of these attacks, with certain elements only taking a few minutes.
According to Microsoft's Security Intelligence team, a recent business email compromise attack (BEC) has shown that threat actors are quickening the pace of these attacks, with certain elements only taking a few minutes.
The rapid attack progression shows that potential victims will have significantly less time to identify any signs of fraud and take preventative measures. BEC attacks primarily use social engineering to impersonate a trusted individual to trick an employee into falling for their trap. One wrong move from a user and your organization could be in crisis mode within minutes of a successful attack.
Microsoft created this timeline of a recent attack that was reported. From the first sign-in to the deletion of the sent email, a total of 127 minutes had passed, reflecting a rush from the attacker’s side:
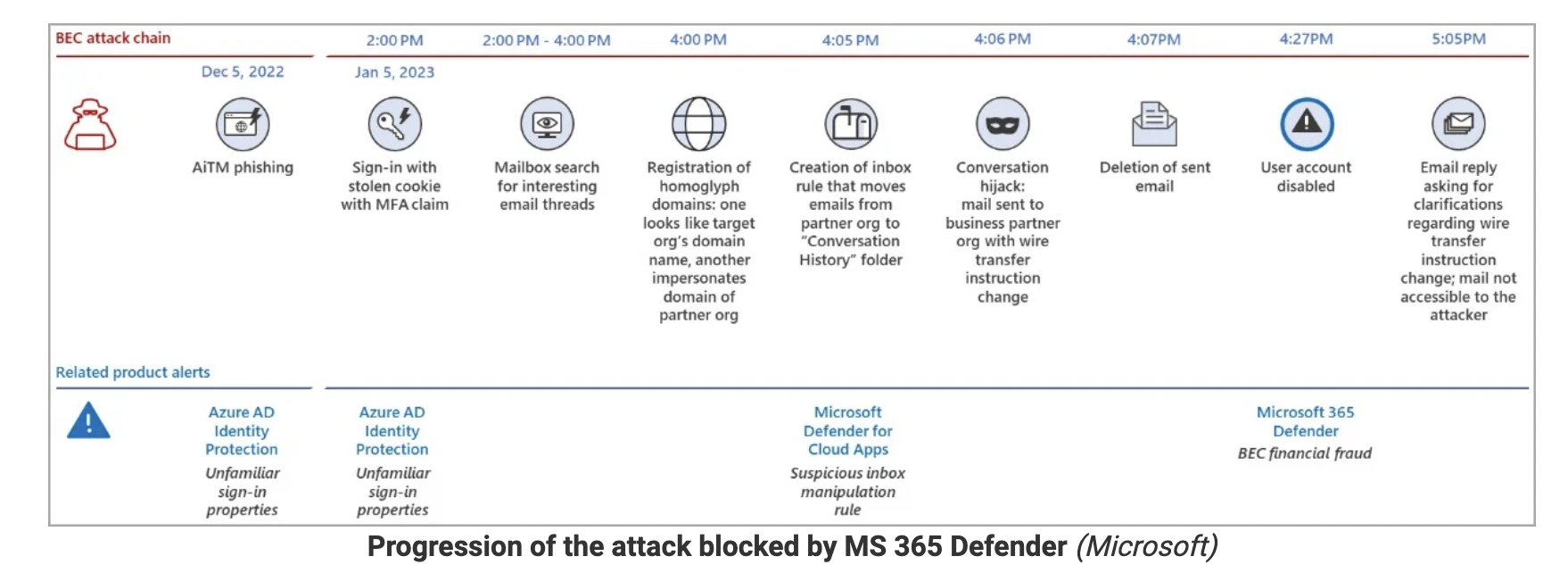
Although Microsoft 365 Defender generated a warning about a BEC attack 20 minutes after the threat actor deleted the sent email and automatically disrupted the attack by disabling the user’s account, there is still barely any time for your organization to respond quickly enough.
Javvad Malik, Security Awareness Advocate at KnowBe4, recently wrote about how BEC attacks should not be overlooked, and I couldn't agree more. New-school security awareness training can ensure your users are prepared to report these types of attacks into their day-to-day operations. Always remember that
your users are your last line of defense!
Bleeping Computer has the full story.
 CEO fraud has ruined the careers of many executives and loyal employees, causing over $26 billion in losses. Don’t be the next victim. This manual provides a thorough overview of how executives are compromised, how to prevent such an attack and what to do if you become a victim.
CEO fraud has ruined the careers of many executives and loyal employees, causing over $26 billion in losses. Don’t be the next victim. This manual provides a thorough overview of how executives are compromised, how to prevent such an attack and what to do if you become a victim.




