Business email compromise (or CEO fraud) has its reconnaissance phase, too. Researchers at Agari say they’ve found that blank, unsolicited emails are often an early sign that a BEC gang is targeting an organization. It serves as a probe to help validate that an email address is likely to be valid, and to be associated with a target the gang in interested in.
Agari’s blog outlines four links in the BEC “attack chain.” They are, in chronological order, “Target Generation,” “Lead Validation and Processing,” “Pre-Attack Testing,” and “BEC Attack.”
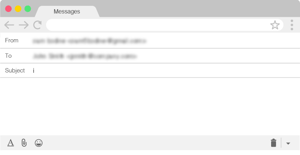
The blank email arrives in the second link. The BEC gang wants a reasonable assurance that its attack will arrive in a live email box. If the blank email, often with only the single letter “i” as its subject, does not bounce, then the criminals proceed with more confidence that they have found a live target.
When they speak of gangs, the researchers mean organized groups of BEC scammers, many of them based in Nigeria and known by such names as “London Blue,” “Scarlet Widow,” and “Curious Orca.” While some of these groups use legitimate lead generation services to verify their targets’ email addresses, Curious Orca’s probing is typically done manually, and they are said to be quite practiced at it.
“Since August 2018, a single Curious Orca associate has sent blank reconnaissance emails to more than 7,800 email addresses at over 3,200 companies in at least twelve countries,” Agaris’s blog post said. “The validated contact information collected by this actor has contributed to a master targeting database containing more than 35,000 financial controllers and accountants at 28,000 companies around the world.”
One protective step Agari recommends is to configure inbound email filters to screen for messages without content. These could then be flagged to a security team for further investigation, and for a timely warning to the targeted individual.
That said, the blank email is also the sort of probe that employees should be aware of. Maybe it was a mistake. Maybe someone just transmitted prematurely. But it would not be out of order for people who receive a blank email to raise their guard. New-school security awareness training is the sort of protective measure that raises awareness of BEC lead validation, and of other steps in social engineering as well.
Agari has the story: https://www.agari.com/email-security-blog/how-bec-scammers-validate-new-targets-blank-emails/
Can hackers spoof an email address of your own domain?
Are you aware that one of the first things hackers try is to see if they can spoof the email address of your CEO? If they are able to commit "CEO fraud", penetrating your network is like taking candy from a baby. 
Find out now if your domain can be spoofed. Request your free Domain Spoof Test so you can address any mail server configuration issues that are found. It's quick, easy and often a shocking discovery. Find out now if your email server is configured correctly, many are not!
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:





