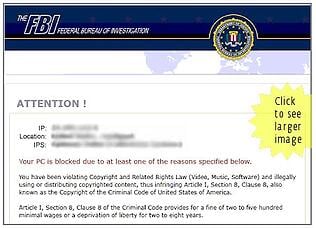
 The Avast Blog reports a new "password stealer" feature in the Reveton ransomware. Reveton is the type of "police" lock/screen ransomware which falsely alerts users they've broken some law and demands payment of a fine, usually in Bitcoin or MoneyPak.
The Avast Blog reports a new "password stealer" feature in the Reveton ransomware. Reveton is the type of "police" lock/screen ransomware which falsely alerts users they've broken some law and demands payment of a fine, usually in Bitcoin or MoneyPak.
The authors upgraded the despised malware from a LockScreen-only version to a powerful password and credentials stealer by adding the last version of "Pony Stealer". This addition affects more than 110 applications and turns your computer to a botnet client. It's a good example of the criminal ecosystem that exists now; malware writers license other malware writer's apps and integrate them for more profit.
The Reveton ransomware has added two password stealers now, they started with the Papras family of malware. Papras is not as effective as Pony but can disable security programs, however the addition of Pony makes it a dangerous combination. Pony authors do deep reverse engineering work which results in almost every password decrypted to plain text form. The malware can crack or decrypt quite complex passwords stored in various forms. Pony is actually very advanced and can pluck and decrypt encrypted passwords for FTP, VPN and email clients, web browsers and instant messaging programs.
Reveton also steals passwords from 5 crypto currency wallets. At the moment, the banking module targets 17 German banks and depends on geolocation but you can expect that to expand rapidly. In all cases, Reveton contains a link to download an additional password stealer. The most common infection vector is via well-known drive-by exploit kits. This means users visiting websites and clicking on links they should not click on is the main cause of this ransomware infection.
Another reason for effective security awareness training, and if a user that is trained using our program infects their workstation with ransomware, we pay your crypto-ransom. Find out how affordable this is for your organization now. Why Kevin Mitnick security awareness training? Ransomware, that's why.





