Trend Micro reported:
Just like other ransomware variants, the Cryptoblocker malware will encrypt files for a specific amount. However, this particular variant has certain restrictions. For one, it will not infect files larger than 100MB in size. Additionally, it will also skip files found in the folders C:\\WINDOWS, C:\\PROGRAM FILES,and C:\PROGRAM FILES (X86).
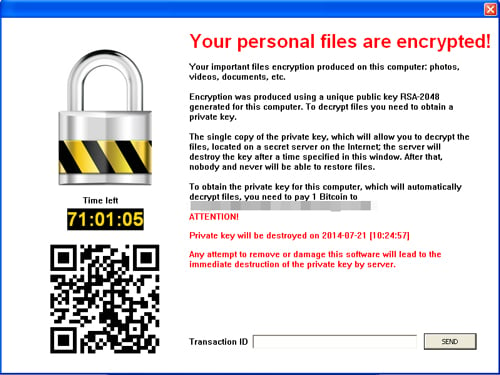
And unlike other ransomware variants, Cryptoblocker will not drop any text files instructing the victim on how to decrypt the files. Rather, it displays the dialog box below. Entering a transaction ID in the text box will trigger a message stating that the “transaction was sent and will be verified soon."
"Another distinction is that its encryption routine is different from Cryptolocker. This malware does not use CryptoAPIs, a marked difference from other ransomware. CryptoAPIs are used to make RSA keys, which were not used with this particular malware. This is an interesting detail considering RSA keys would make decrypting files more difficult. Instead, we found that the advanced encryption standard (AES) is found in the malware code.
"A closer look also reveals that the compiler notes were still intact upon unpacking the code. This is highly interesting as compiler notes are usually removed. This is because this information could be used by security researchers to detect (and thereby block) files from the malware writer. The presence of the compiler notes would suggest that perhaps the bad guy behind Cryptoblocker is new to the creation of ransomware.
More at TrendMicro's Blog




