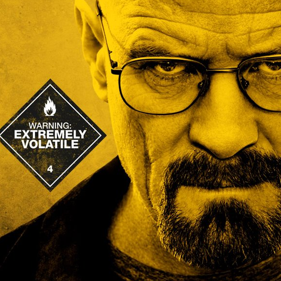
 With the TV show Breaking Bad in its last season, this seems to be a fun title. However, the topic is not all that much fun. You should realize it's not a question of when you will be compromised. It is a question of when you will discover you have been compromised. That means IT security is really about if you can detect, respond and quickly resolve compromises. It is actually a safe bet to assume that your network is already owned, you just don't know about it (yet).
With the TV show Breaking Bad in its last season, this seems to be a fun title. However, the topic is not all that much fun. You should realize it's not a question of when you will be compromised. It is a question of when you will discover you have been compromised. That means IT security is really about if you can detect, respond and quickly resolve compromises. It is actually a safe bet to assume that your network is already owned, you just don't know about it (yet).
To protect your network against monitoring by either foreign attackers or rogue agencies in your own country, you are going to need a top-down security culture, and not rely on just your run-of-the-mill IT security hardware and software. For instance, you're going to have to have a serious look at wall-to-wall encryption. It is tough to get your wits wrapped around the fact that highly likely each of your IT security software and hardware appliances all have dozens and possibly hundreds of vulnerabilities that some people know about and can exploit.
All this means your C-Level execs need to be aware of the risks, your whole defense-in-depth stack needs to be in place and that means you also need to pay (a lot of) attention to Policy, Procedure and Awareness which is the outer layer of defense-in-depth. Here is a 1-minute explanation:
Being lax with the Policy and Procedure layer is what caused the NSA to get #snowdened. Going forward in the future and being reasonably sure that your databases and intellectual property is not compromised means getting your IT Security fundamentals in place and getting it right. We are soon releasing a 15-minute security awareness training for C-level Execs and Middle Management about APT and how they can protect themselves against this. It will help to make them aware of the need for a Top-down security culture. Stay tuned!




