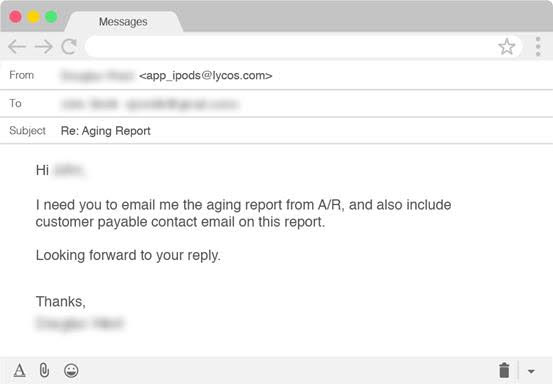
Business Email Compromise—also known as CEO Fraud—scammers are now targeting a company's customers using a new indirect attack method designed to collect information on future scam targets by asking for aging reports from collections personnel.
Aging reports, also known as a schedule of accounts receivable, are sets of outstanding invoices which allow a company's financial department to keep track of customers who haven't yet paid services or goods they were allowed to buy on credit.
"It’s an essential tool for both accounts and management to maintain an overview of their credit and collection processes, and breaks down outstanding debts into thirty-day increments, culminating with payments that are more than ninety days overdue," says Agari threat researcher James Linton.
BEC (also known as Email Account Compromise - EAC) fraud schemes are scams through which crooks trick organizations' employees into wiring money to entities they trust but whose bank accounts were swapped with ones controlled by the crooks.
BEC attacks have seen an explosive Q4 476% YoY growth
The attackers have been intercepted by Agari Cyber Intelligence Division (ACID) while posing as CEOs of targeted companies and requesting information from employees on invoices that are overdue for payment in the form of an aging report.
Name deception and free email accounts were used by the crooks in their attempt to deceive company employees to follow up to their demand for company records.
Not asking for payments straight out is exactly what makes this new BEC attack so unusual seeing that, in most other similar scams, financial department employees are asked to send payments to attacker-controlled bank accounts.
BEC attacks have also seen an explosive 476% growth between Q4 2017 and Q4 2018, with the total number of email fraud attempts against organizations increasing by 226% QoQ as detailed in a Proofpoint report from January. Story at Bleepingcomputer:
Get Your CEO Fraud Prevention Manual
 CEO fraud has ruined the careers of many executives and loyal employees. Don’t be next victim. This manual provides a thorough overview of how executives are compromised, how to prevent such an attack and what to do if you become a victim.
CEO fraud has ruined the careers of many executives and loyal employees. Don’t be next victim. This manual provides a thorough overview of how executives are compromised, how to prevent such an attack and what to do if you become a victim.
PS: Don't like to click on redirected buttons? Copy and paste this link in your browser:
https://info.knowbe4.com/ceo-fraud-prevention-manual





