The bad guys are now exploiting news of the CapitalOne breach to push a malicious backdoor trojan via a phishing email purporting to offer a Windows Security Update. See the attached example email.
Clicking the link in that email downloads a file named KB3085604.exe — obviously named to resemble Microsoft patch files and security updates. Detection of this file by the anti-malware engines represented on VirusTotal is poor, with only nine flagging it at this point.
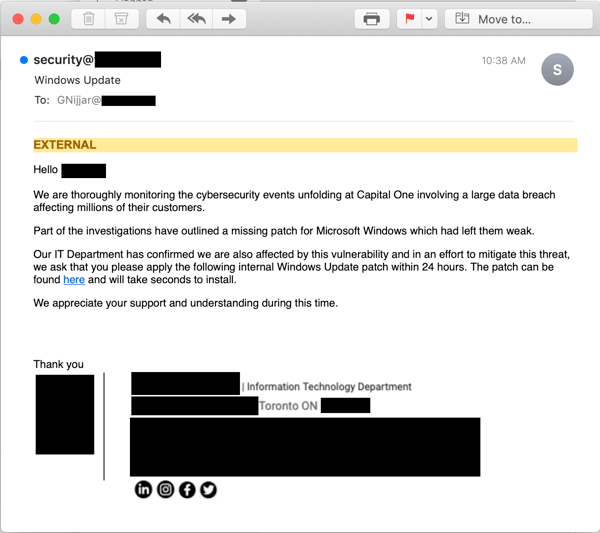
The phishing email itself spoofs the targeted organization’s IT department, and the language used is sufficiently informal (as well as a little technical and even awkward) to appear credible.
As a result, some users just might fall for it — esp. those working in organizations that occasionally ask employees to perform routine IT tasks (e.g., applying updates, updating AV definitions, etc.).
Now is the time to warn your users and ensure that they know how to distinguish actual, legitimate email notifications sent by your IT Department or Help Desk from malicious imposters like this latest phish.
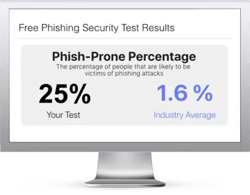
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before the bad guys do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
 Here's how it works:
Here's how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:





