You are probably aware of the terms SIGINT (signals intelligence, like radio interception) and HUMINT (human intelligence, like espionage). There is a new term coined by the University of Washington called ADINT which shows how anyone can track what apps an employee uses and where they have been—for just $1,000—and can be used for social engineering attacks.
A team of computer science engineers at UW learned that obtaining an employee's smartphone’s mobile advertising identification, known as a MAID, would open the door to all the information advertisers use to serve promotional materials. The study is titled "Using Ad Targeting for Surveillance on a Budget."
"It’s not a particularly high bar to entry for a very, very highly targeted attack," says Adam Lee, a professor at the University of Pittsburgh who reviewed the University of Washington study. The University of Washington will present its findings in Dallas on Oct. 30 at Association for Computing Machinery’s Workshop on Privacy in the Electronic Society.
The attacks could use data like an employee's personal interests, dating habits, religion, health conditions, political status, the apps they use and possibly, even more.
It’s also disturbingly easy for the bad guys to learn a user's MAID. They can simply gain access to a Wi-Fi router or eavesdrop on an unsecure Wi-Fi network.
MAID lets advertising companies and others with your MAID track your movements. Once the MAID is obtained, criminal hackers would offer the user malicious ads based on their location, compromising the mobile device.
This kind of advertising is often how free apps make a profit. Some services urge users to provide location data they can then sell to advertisers. Snapchat’s privacy policy, for example, says your location is used for “ad targeting and measurement, including through the use of your precise location data.”
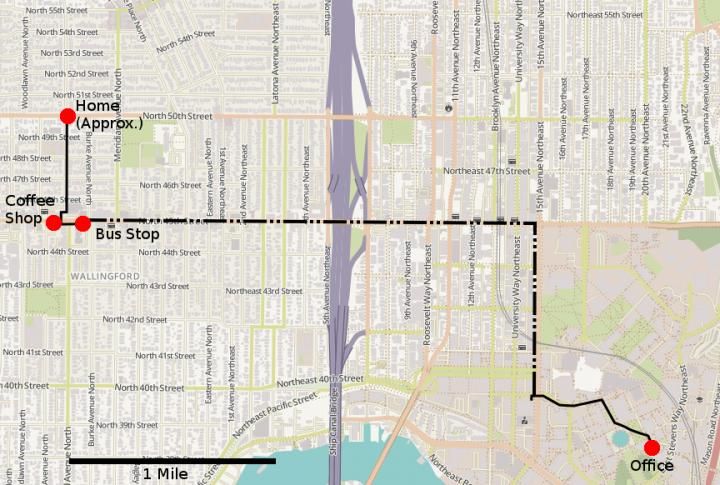
Importantly, the target does not have to click on or engage with the ad -- the purchaser can see where ads are being served and use that information to track the target through space. In the team's experiments, they were able to pinpoint a person's location within about 8 meters, just over 20 feet.
Here is how to warn your users
I recommend you cut & paste this and email it to your users. Feel free to edit:
Bad guys can use your smartphone to target you and find out where you physically are. Here are three steps you can take to protect yourself:
- Do not grant location access to any apps unless 100% necessary.
- Try keeping your mobile data safe by browsing only on protected Wi-Fi networks to limit the amount of confidential data you release.
- Do not click on any ad banners that are being displayed on your phone. It is very hard to know if these banners are malicious or not.
I strongly suggest you get a quote for new-school security awareness training for your organization and find out how affordable this is. You simply have got to start training and phishing your users ASAP both on their workstation and mobile devices. If you don't, the bad guys will, because your filters never catch all of it. Get a quote now and you will be pleasantly surprised.





