 I blogged a few days ago about a method to embed a crypto-mining script in a Word doc. Turns out an ad network has done an even better job!
I blogged a few days ago about a method to embed a crypto-mining script in a Word doc. Turns out an ad network has done an even better job!
Arstechnica wrote: "Domain-name algorithms are a software-derived means for creating a nearly unlimited number of unique domain names on a regular basis. DGAs, as they're usually called, came to light in 2008 following the release of the highly viral Conficker worm.
To prevent whitehats from seizing the domain names Conficker used to receive command and control instructions, the malware generated hundreds of new, unique domains each day that infected computers would check for updates. In the event that old domains were sinkholed, Conficker needed to reach only one of the new addresses for it to remain under its creator's control.
The burden of registering more than 90,000 new domain names every year has proved so great to whitehats that Conficker continues to operate even now.
Researchers at China-based Netlab 360 reported over the weekend that an advertising network is using DGAs to conceal the in-browser currency-mining code it runs on websites.
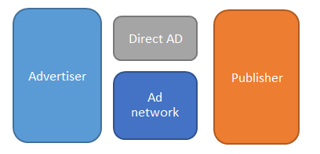
Normally, the ad network will redirect visitor browsers to serve.popad.net, which hosts ads that load coinhive.min.js. That's the JavaScript code that bogs down visitor computers by making them participate in a giant mining pool hosted by coinhive.com, which keeps 30 percent of the proceeds and gives the remainder to the advertiser or website that provided the referral.
In most cases, all of this happens behind the scenes with no visible sign of what's happening, with the exception of over-revving fans and decreasing computer performance.
Let's train end-users to not click on ads in browsers.
Full story at: https://arstechnica.com/information-technology/2018/02/ad-network-uses-advanced-malware-technique-to-conceal-cpu-draining-mining-ads/
The above makes a very strong case for a brand new look at your last line of defense, your users.
It makes all the sense in the world to transform them into a human firewall ASAP, and keep them on their toes with security top of mind. Step them through new-school security awareness training which combines on-demand interactive, engaging web-based training with frequent simulated phishing attacks right in their inbox. This is a very effective approach, with the best ROI of practically any IT security tool. We have just received a Forrester Total Economic Impact report that shows an ROI of less than a month.
Don't like to click on redirected buttons? Copy and paste this in your browser: https://info.knowbe4.com/training-request-a-demo
Prepare to be pleasantly surprised...
Warm regards,
Stu Sjouwerman
Founder and CEO, KnowBe4, Inc






