/Phishing-T.jpg?width=200&name=Phishing-T.jpg) Most companies have not implemented standards for authenticating emails and preventing hackers from successful phishing attacks, according to Valimail.
Most companies have not implemented standards for authenticating emails and preventing hackers from successful phishing attacks, according to Valimail.
Businesses and consumers see more than 1.2 million phishing attacks each year, as hackers use the effective social engineering attacks to con employees into clicking a malicious link or attachment. Despite how widely known and damaging these attacks can be, companies still fail to adequately prevent them from happening, according to a Friday report from Valimail.
Widely-accepted open standards exist for authenticating email and preventing phishers from spoofing domains with fake emails, but a majority of companies across industries have not made full use of them. The vast majority—90%—of large tech companies remain unprotected from impersonation (CEO Fraud) attacks, the report found.
The report examined the primary domains for 525 global tech companies with revenues of more than $500 million annually, querying them for the presence of Domain-based Message Reporting, Authentication & Conformance (DMARC) records and Sender Policy Framework (SPF) records.
Nearly half (49%) of companies had DMARC records of some kind, indicating that they have begun to deploy this anti-phishing tool. But only about half (55%) of those companies have DMARC records that were correctly configured and set to a policy that will actually stop phishing and spoofing, the report found.
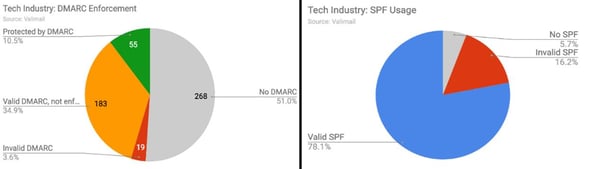 Companies are more advanced when it comes to SPF, the report noted, likely because it is older and better understood. Some 78% of tech companies analyzed are using SPF correctly, it added.
Companies are more advanced when it comes to SPF, the report noted, likely because it is older and better understood. Some 78% of tech companies analyzed are using SPF correctly, it added.
The presence of DMARC is positively correlated with a company's revenue, according to the report: Companies with DMARC enforcement had an average revenue of more than twice that of companies with no DMARC records at all, at $10.2 billion versus $5 billion. Both TechRepublic and Bleepingcomputer had the story.






