 New data shows just how impactful these attacks are, with 98% of victim organizations reporting some form of impact from email-based cyber attacks.
New data shows just how impactful these attacks are, with 98% of victim organizations reporting some form of impact from email-based cyber attacks.
We all know a successful cyber attack will result in some degree of damage. But quantifying that is difficult; you likely have response, recovery and mitigation plans in place (and, if you don’t, get started!), but you should also have some idea of potential monetary damages from an attack.
Barracuda’s new 2023 Email Security Trends report puts those impacts into very quantifiable terms, helping security teams and C-suites better plan for what should be seen as inevitable.
According to the report, the percent of organizations that are experiencing some degree of impact has risen from 74% (in 2019) 98% in 2023. The fact that almost every organization experienced some kind of impact means you will too.
So, what should you expect?
According to the report, two of the most common and most expected are downtime and loss of data. Given that ransomware remains the top cyberattack and 96% of them include exfiltration of data, this all makes sense. But, as shown below, there are plenty of other impacts – the least, of which, is recovery costs.
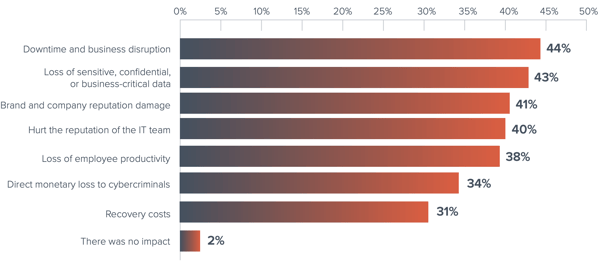
Source: Barracuda
Since email-based attacks require the interaction of the recipient user to enable the attack, putting new school Security Awareness Training in place it should be a critical part of your cybersecurity strategy.
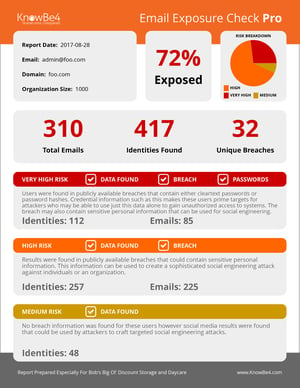 Here's how it works:
Here's how it works:




