 Sophos released their 2018 malware forecast this week. Their predictions would make any IT Pro concerned, a PDF of their report is here. Read on for your executive summary.
Sophos released their 2018 malware forecast this week. Their predictions would make any IT Pro concerned, a PDF of their report is here. Read on for your executive summary.
Ransomware Mutations Running Amok
You have seen a lot this year about in this blog about the WannaCry and NotPetya ransomware strains.
Both attacks exploited the EternalBlue Windows SMB vulnerability, and both did not have workable decryption mechanisms for the few organizations desperate enough to try to pay the ransom.
Both incidents make one thing clear: WannaCry and NotPetya appear to be the work of military cyber warfare divisions. Their authors aren't script kiddies, but professional Dev teams using sophisticated techniques. Nation states are fighting a cold cyber war, and commercial and non-profit organizations are the collateral damage worldwide.
RaaS Is For Newbie Cyber Crims
There is an area where amateur cyber "crims" do come in, and that's Ransomware as a Service, aka RaaS. Newbies without a lot of skills simply buy the code on the dark web including instructional how-to videos.
Sophos says that RaaS is growing in popularity on the Dark Web, and this year's Cerber ransomware is their example of a worrisome trend. Here's some of what it says in the report that specifically pertains to RaaS:
“Ransomware is big business on the Dark Web. Its creators realized they could make more money not just by extorting currency from their victims, but by selling kits buyers could use to make and distribute their own. We’ve seen a number of different services and pricing models in the past year, and expect to see many more in 2018.
One of the biggest examples, as mentioned above, is Cerber. Other examples include Satan, malicious software that once opened in a Windows system, encrypts all the files and demands a ransom for the decryption tools, and Philadelphia. The latter was notable for its marketing technique, which included a slick YouTube video advertisement on the open web.”
New "Marketing" Techniques
Sophos reports on an additional ransomware trend they found in a malware strain called Spora. Instead of demanding one ransom to decrypt an entire encrypted drive or partition, some ransomware offers victims multiple options. The options seen in Spora are:
- Decrypt two files for free
- Decrypt a selection of files for $30
- Have the ransomware itself removed for $20
- Buy what they call immunity for $50
- Get everything on the computer restored for $120
Ransomware Is Now Targeting Non-Win OSen
September 2013 was when Cryptolocker reared its ugly head as the first weapons-grade ransomware that exclusively targeted Windows, which remains Target No. 1.
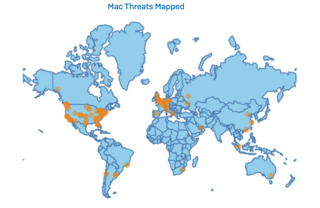
But Sophos notices a trend of ransomware targeting non-Windows operating systems. I would not be surprised if in 2018 a worldwide MacOS or Linux distro ransomware pandemic broke out.
Ransomware is also growing rapidly on Android. Sophos reported that the prevalence of Android ransomware has grown almost every month in 2017; 30.4% of the Android malware researched in September 2017 by Sophos was ransomware, and they expect that 45% of all Android malware in October was ransomware.
One of the biggest Android ransomware stories broke this October: DoubleLocker. Looks like Android ransomware is going to be a bigger problem in 2018.
Healthcare Continues To Be A Target.
Many cyber criminals are specifically targeting the healthcare industry. Sophos states this trend started in 2016. Healthcare is the single most targeted industry because they are the victims who are most likely to pay the ransom. The Sophos report shows that critical infrastructure, education and small businesses also are often targeted for ransomware attacks, as they're more likely to pay up as well.
Between April 1st and October 3rd, Sophos notes that the top four countries for ransomware victims are the United States (17.2%), Great Britain (11.1%), Belgium (8.6%), and Singapore (6.5%.) And of course neither Ukraine or Russia even show up in the Top 16, because that's where these organized cyber crime gangs are, and they know that FSB swat teams will knock down their doors if they target these countries.
Free Ransomware Simulator Tool
How vulnerable is your network against a ransomware attack?
Bad guys are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
KnowBe4’s "RanSim" gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 13 infection scenarios and show you if a workstation is vulnerable to ransomware infection.





