 One of the greatest inventions in modern history is the Reese’s Peanut Butter Cup. I feel sorry for any human who existed before the “age of the cup” because they never got to know the delicious glory that accompanies the unification of chocolate and peanut butter. Previous to that time, people walked around in total ignorance thinking that they had to make an “either/or” decision related to these two approaches to snack-based nourishment. And then a revelation happened that may have been something like this 1972 commercial for the product: https://www.youtube.com/watch?v=GuENAWds5B0.
One of the greatest inventions in modern history is the Reese’s Peanut Butter Cup. I feel sorry for any human who existed before the “age of the cup” because they never got to know the delicious glory that accompanies the unification of chocolate and peanut butter. Previous to that time, people walked around in total ignorance thinking that they had to make an “either/or” decision related to these two approaches to snack-based nourishment. And then a revelation happened that may have been something like this 1972 commercial for the product: https://www.youtube.com/watch?v=GuENAWds5B0.
Now, here’s the funny thing. Somehow even in a world that has been graced by the peanut butter cup, many people still believe that decisions have to be binary. Such people believe that, because they are naturally drawn to one of the ways of addressing a problem, then other ways of addressing the problem must be invalid.
IT vendors and security pundits also fall into the trap. An example of this came to my attention just a couple days ago when I came across a Forbes ‘article’ entitled: Technology not Training Protects Users from Phishing. First-things-first, the author of the article – a Google employee within their Office of the CTO -- is obviously a very intelligent individual… I’m not debating that at all. But I will call-out the fact that the ‘article’ is actually part of a paid marketing effort by Google to promote Google’s approach to mitigating phishing via technology.
There are other issues with the article and argument as well. Specifically, the author uses the term phishing very broadly to make sweeping statements about where technology can assist in mitigating the phishing threat. But it turns out that he is really only discussing “credential harvesting” phishing attacks… and his answer is multifactor authentication (MFA) instead of training.
And here’s the problem: he said that we need to ditch all phishing training and adopt MFA. But what about phishing attacks that aren’t after a user’s credentials? MFA doesn’t help with that. What about phishing attacks that are all about tricking users into clicking links or downloading attachments with the intent of infecting their computer with malware? What about phishing emails with no links or attachments whatsoever (BEC, anyone???)? And what about situations where users are working in situations where MFA isn’t an option, like some of their home systems? Or when users forget their MFA key so the app then allows for knowledge-based authentication (KBA)?
Here’s the thing: MFA is a great help. It can drastically reduce the effectiveness of credential harvesting attacks. But it is not – and will likely never be – a full ‘fix’ for phishing and social engineering.
Could that be why Google seems to be arguing with itself? Here’s a Google blog from just two months ago by Google Security & Anti-abuse Research Lead, Elie Bursztein and Daniela Oliveira, Professor at the University of Florida. They highlight the importance of training and awareness and end with the following statement:
“While technologies to help mitigate phishing exist, such as FIDO standard security keys, there is still work to be done to help users increase awareness understand how to protect themselves against phishing.”
-- Elie Bursztein, Security & Anti-abuse Research Lead, Daniela Oliveira, Professor at the University of Florida
What we’ve seen throughout history is that criminals are persistent. When they are stymied by technology-based defenses, they will find a way to go around the technology and exploit a human vulnerability. The way that they do that typically involves social engineering (phishing). And so, having MFA is something I recommend… but it doesn’t mitigate the impact of phishing. Because if I’m an attacker, I can adjust my attack and try a different type of phish.
Luckily, not every technology vendor falls into the techno-centric trap. Here’s a great example from a recent Microsoft blog post. In the blog, Girish Chander Group Program Manager, Office 365 Security, outlines the Top 6 email security best practices to protect against phishing attacks and business email compromise. (https://www.microsoft.com/security/blog/2019/10/16/top-6-email-security-best-practices-to-protect-against-phishing-attacks-and-business-email-compromise/). One of his points is all about the importance of training your users. Here’s what he says:
Your users are the target. You need a continuous model for improving user awareness and readiness.
An informed and aware workforce can dramatically reduce the number of occurrences of compromise from email-based attacks. Any protection strategy is incomplete without a focus on improving the level of awareness of end users.
A core component of this strategy is raising user awareness through Phish simulations, training them on things to look out for in suspicious emails to ensure they don’t fall prey to actual attacks.
A quote from the introduction to Bruce Schneier’s book Secrets & Lies comes to mind: “If you think technology can solve your security problems, then you don't understand the problems and you don't understand the technology.” The answer for phishing isn’t technology or training in the same way that the answer for snacking doesn’t have to be chocolate or peanut butter. A layered approach to security is the key to making your organization a hard target. And your human layer is critical to the success of that strategy.
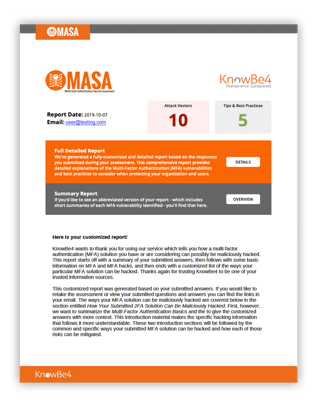 Here's how MASA works:
Here's how MASA works:




