
The ransomware market is rapidly maturing, we start seeing upgraded strains and rebranded versions sold cheaply in the Dark Web. And mainstream media have finally glommed on after years of being oblivious, trumpeting the FBI recently projected that the losses caused by ransomware infections could reach a billion dollars in 2016 alone. Here is your July Ransomware Roundup.
Upgraded Strains
You, yes, YOU could be an infection vector, making your customers a ransomware victim.
The leading cybermafias are furiously innovating to stay ahead of the copycats. Cerber has updated its code numerous times, like adding a DDoS and the use of double-zipped Windows Script Files (WSFs) to evade detection, July saw the release of Cerber’s latest variant that put Office 365 users in homes and in businesses at the crosshairs of attack. The attack vector? Phishing with Office documents laced with macros and once your user opens on the attachment, Cerber encrypts 442 file types using combined AES-256 and RSA encryption. This new strain was also pushed by the Rig and Magnitude exploit kits which both are using 0-day vulnerabilities.
Padcrypt
After 4 months of not seeing a new version of the PadCrypt Ransomware, a new sample was discovered. This ransomware will encrypt your files and add the .padcrypt extension to them. (Hat Tip to Larry Abrams at Bleepingcomputer.)
Two Ransomware Strains Are Copycats of Earlier Families
CrypMIC
The moment CrypMIC was found, malware researchers immediately saw it was a copycat of CryptXXX, trying to rake in bitcoin with a copied entry point, ransom note, and even its payment user interface. One twist is that CrypMIC does not append any extension name to files that it has already encrypted, which makes it hard to spot which of the files have been affected.
New Blood: Brand New Strains
Satana - New Hybrid MBR Strain
is a blend between classing file encryption malware and the Petya / Misha strain which locks the Master Boot Record (MBR). This looks like a Petya copycat, for each encrypted file, Satana prepends their email address to each file like this: "email@domain.com_filename.extension".
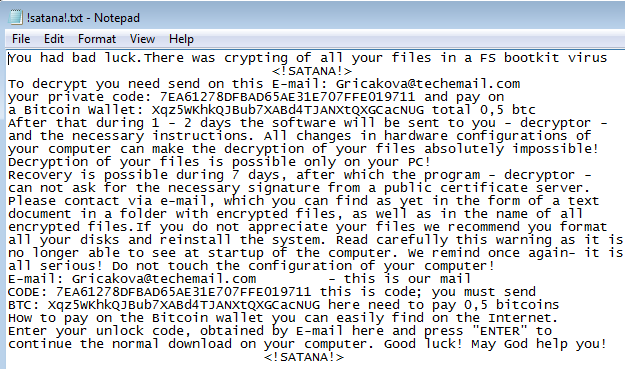
Satana then encrypts the MBR and replaces it with its own. The first time when a user reboots their workstation, Satana's MBR boot code will load and the only thing the machine will show is Satana's ransom note. Here is how the note looks as a text file:
Security researcher Hasherezade posted the initial discovery at Malwarebytes, and stated it might be possible to recover the original MBR. That does not mean you can decrypt the files though. Recovering MBR records via Windows' cumbersome command-line interface is not for the weak of heart. Paying the ransom is a crapshoot, "because you do not know if the C&C server went offline when encryption happened," she writes. According to the Hasherazade, the code looks like a work-in-progress, as its developers are still working on it. Stay tuned, this puppy might cause some damage.
New Zepto Is A Kleptomaniac Locky Spinoff
The new Zepto strain is a monster. It's spewing out spam messages at an alarming rate, and looks very much like Locky, which in itself is a bad sign because it could be the very same cyber mafia and these guys are very sophisticated.
Locky is a dangerous as-yet unbroken ransomware that helped the authors of the Nuclear exploit kit to score US$12 million in revenue from 1.8 million attacks cast over one month. Monthly income for developers sits around US$100,000. Here is a short video of an anti-ransomware product which blocks Zepto: https://youtu.be/ZycM5ULBK4M
Cisco's Talos researchers are particularly concerned that Zepto will move into exploit kits and that attackers will move on from spam to other distribution methods, such as malvertising, according to ThreatPost.
EduCrypt Ransomware Teaches Users A Much Needed Lesson?
EduCrypt is based on the Hidden Tear ransomware strain. EduCrypt encrypts only a small part of the file and folders and it doesn’t communicate with a Command & Control server. EduCrypt is basically harmless and intends to teach users a lesson, but it's "shock therapy" and causes a lot of lost time for IT people to fix it.
Educrypt uses an extension list and files will be encrypted with a static password of HDJ7D-HF54D-8DN7D, and the encrypted files have the .isis file extension. Once the encryption process ends a note called README.txt is created on the desktop and the note also comes with a link to the decryptor.
An infection with EduCrypt is still a major hassle and you could see it as a shot across the bow to make sure you have all security layers in place to make sure this does not happen with the real thing.
Other new strains spotted in July:
- CryptoFinancial was discovered by Malwarebytes security researcher S!Ri. This malware pretends to be a ransomware program that encrypts your files, but instead will delete your files and not provide a way of recovering them. A new ransomware called Bitstak was discovered by MalwareHunterTeam. This ransomware has very interesting, if not laughable, programming that allowed Michael Gillespie to create a decryptor for it.
- PizzaCrypts has been discovered by security researcher Brad Duncan. This ransomware is currently spreading via the Neutrino Exploit Kit and when it encrypts your files it will append the .id-[victim_id]-maestro@pizzacrypts.info extension to their filenames.
- cuteRansomware uses Google Docs and other cloud apps to transmit encryption keys and gathering user information to evade detection.
- Alfa ransomware looks like a descendant of Cerber, the malware scans its infected system’s local drives and encrypts over 142 file types, appending a “.bin” extension name to the locked file.
- CTB Faker copycats CTB Locker. This variant is spread via bogus profiles from adult sites that trick users with the promise of access to a password-protected striptease video. The poisoned link then leads to the download of the ransomware hosted on JottaCloud.
- Ranscam was also discovered in July, which threatens to delete files unless a 0.2 bitcoin-ransom is paid. The tricky part, though, is that the files are deleted even if the ransom has already been paid for, probably buggy code so wait for the next version to fix that.
4x Growth In Android Ransomware Attacks
New numbers published by Kaspersky found that the number of ransomware attacks on their Android users from April 2015 to March 2016 had quadrupled compared to the same period 12 months prior. The Fusob family of ransomware was responsible for over half of all reported attacks. (Tripwire)
All The Strains Rely On Social Engineering
You simply cannot sit back and hope your filters are going to catch it all, they never do. You have to create an additional layer, call it your "human firewall". Thousands of organizations are doing this with great results. You have to do this anyway to be PCI compliant so why not do it right the first time?
Stepping your users through new-school security awareness training is a must, moreover it's simply fun to phish your users and train them not to fall for social engineering attacks!
 Here's how it works:
Here's how it works:




