 Malicious actors continue to craft ruthlessly aggressive, evil email attacks tailored to leverage mounting fears and anxieties surrounding the COVID-19 outbreak in the United States among employees in the office and at home.
Malicious actors continue to craft ruthlessly aggressive, evil email attacks tailored to leverage mounting fears and anxieties surrounding the COVID-19 outbreak in the United States among employees in the office and at home.
In the latest Coronavirus-themed phishing email reported to KnowBe4 by customers using the Phish Alert Button (PAB), bad guys try to exploit the very worst fear among email recipients: the fear of infection.
Hitting the Panic Button
Late Friday night March 27, 2020, we spotted a new phishing email warning the recipients that they have been exposed to the Coronavirus through personal contact with a "colleague/friend/family member" and directing them to download a malicious attachment and proceed immediately to the hospital.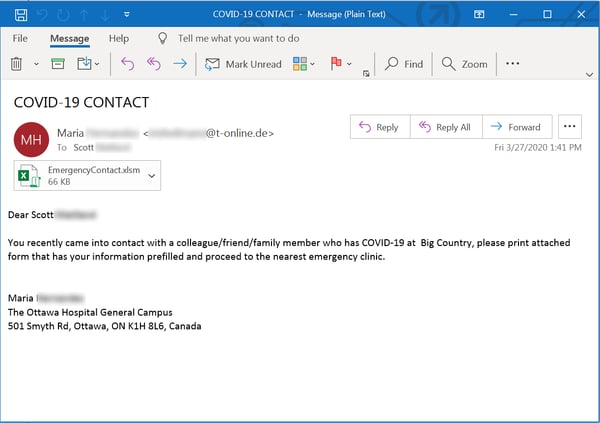
This email is simple, succinct, and alarming. Moreover, it spoofs a hospital, lending additional credibility to this particular social engineering scheme, which is clearly designed to elicit a panicked response from readers and override any form of rational, measured thought.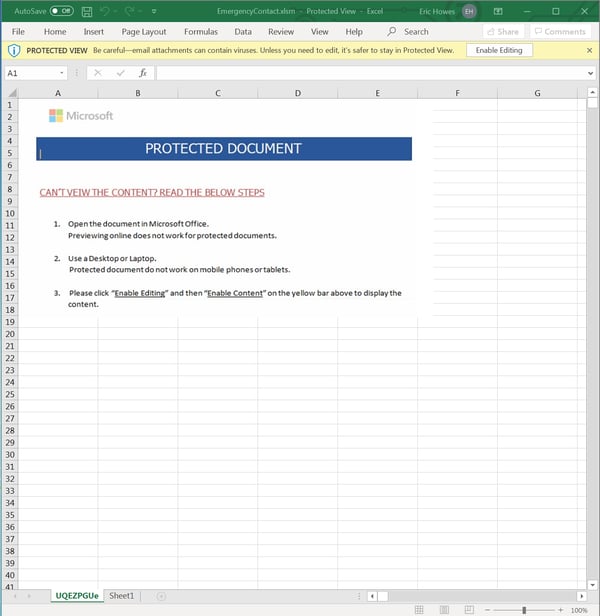
The attached Excel file is billed as a "pre-filled" form that victims should bring with them to the hospital. In fact, that form is a malicious, macro-laden Office document that serves as a trojan downloader and is currently detected by only a handful of major anti-virus applications.
Users who make the mistake of following the directions provided in that Excel file and enable macros will be kicking off a download process for a sophisticated and dangerous backdoor trojan that currently enjoys a moderate (though rising) number of detections among the anti-malware engines represented on VirusTotal.
This fairly nasty piece of malware (first reported to VirusTotal on Mar. 27, 2020) sports a number of advanced functions that allow it to evade detection by security applications, worm its way deep into an infested system, and serve as a platform for a variety of criminal activities.
Conclusion: Five High-Priority Recommendations
Many organizations are in the process of enabling their users to work from home securely. Apart from having and enforcing a remote work security policy, we strongly recommend to deploy the following high-priority elements of these urgent projects:
- a VPN;
- Single Sign On (SSO) fortified by;
- Multi Factor Authentication (MFA);
- An Immediate And Vigorous Security Awareness Training Campaign
- Fully patched machines in the cloud, the office and at the house
The COVID-19 outbreak in the United States has provided malicious actors with an unprecedented opportunity to weaponize widespread fears and concerns among the general public for the purposes of social engineering schemes prosecuted through malicious emails. For the bad guys, this is the ultimate in target-rich environments.
As rapidly mounting infections in United States drive a growing climate of fear, employees need to be educated and trained to expect these kinds of emails, accurately identify them, and handle them safely.
 New-school Security Awareness Training is critical to enabling you and your IT staff to connect with users and help them make the right security decisions all of the time. This isn't a one and done deal, continuous training and simulated phishing are both needed to mobilize users as your last line of defense. Request your quote for KnowBe4's security awareness training and simulated phishing platform and find out how affordable this is!
New-school Security Awareness Training is critical to enabling you and your IT staff to connect with users and help them make the right security decisions all of the time. This isn't a one and done deal, continuous training and simulated phishing are both needed to mobilize users as your last line of defense. Request your quote for KnowBe4's security awareness training and simulated phishing platform and find out how affordable this is!




