 CyberheistNews Subscriber Stuart Sanders sent me this: "A friend of mine in Melbourne Australia has been whacked by several crypto attacks on his clients in the last week. He supports accountants, just accountants nothing else."
CyberheistNews Subscriber Stuart Sanders sent me this: "A friend of mine in Melbourne Australia has been whacked by several crypto attacks on his clients in the last week. He supports accountants, just accountants nothing else."
Here is an example 2-stage attack which shows how highly personalized these ransomware attacks are getting. Note the language is getting better, but is not perfect.
STAGE 1
Hello,
You have been recommended by a friend as a reliable firm to handle my company and personal financial plans.
Before I visit your office I will like for you to go through my portfolio so that you can go through and make appointment to make things easier as I am a very busy person. You can refer me to the person to go through this for me.
I will appreciate your fast response.
Stuart Hazell
STAGE 2
Once the bad guys received a response from a potential victim regarding the first email, they then send a second email with a link to the documents that they want to "share" with the accountant and this is where the attack is happening.
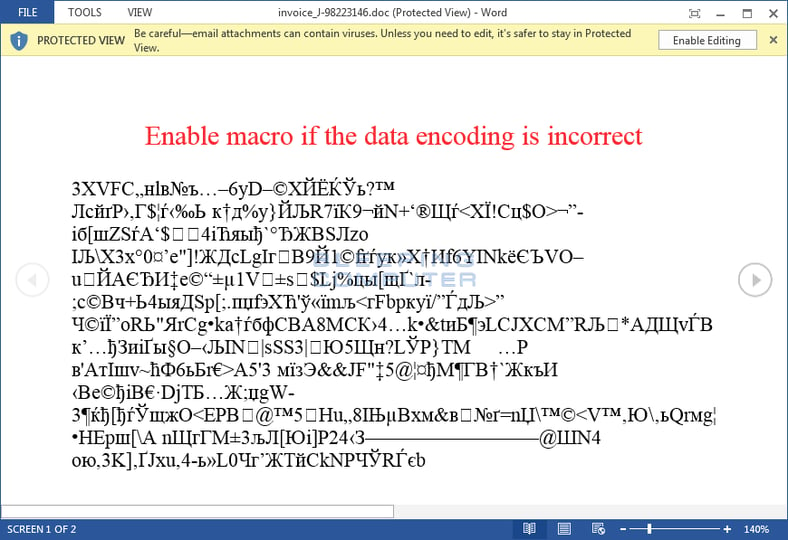
This is possibly automated, we cannot say for sure if that is the case or not. The documents are in all cases malicious and infected with ransomware. Opening the document and clicking "enable editing" activates macros that will kick off the ransomware code. Here is an example of how that can look:
Regularly warn your users that they remember to never open any attachment they did not ask for, especially if it is from a stranger that they have not communicated with before.
Free Phishing Security Test
Did you know that 91% of successful data breaches started with a spear-phishing attack?
Cyber-attacks are rapidly getting more sophisticated. We help you train your employees to better manage the urgent IT security problems of social engineering, spear-phishing and ransomware attacks. Take the first step now. Find out what percentage of your employees are Phish-prone™ with our free test. Did you know that KnowBe4 also supports "Vishing" where you can actually send your users simulated voice mail attacks?

PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://www.knowbe4.com/phishing-security-test-offer




