
Apart from me, guess who has been anticipating the Disney+ channel?
Right. The Bad Guys. I admit I'm a Marvel Universe fan, and could not wait for Disney+ to come out. The first thing I watched were the two episodes of the Mandalorian... promising!
Disney started their video streaming service this week in America, Canada and Holland. They also announced four more Marvel movies for 2020 which all will be available through Disney+. They signed up more than 10 million users in their first 24 hours.
However, there were quite a few "teething" problems and hidden in the flood of tech support tickets was a malicious unexpected problem.
Hackers didn't waste any time and have started hijacking Disney+ user accounts mere hours after the service launched. The speed at which hackers have mobilized to monetize Disney+ accounts is astounding. Accounts were put up for sale on hacking forums within hours after the service's launch.
 Many of these accounts are now being offered for free on hacking forums, or available for sale for prices varying from $3 to $11, a ZDNet investigation has discovered. Many users reported that hackers were accessing their accounts, logging them out of all devices, and then changing the account's email and password, effectively taking over the account and locking the previous owner out.
Many of these accounts are now being offered for free on hacking forums, or available for sale for prices varying from $3 to $11, a ZDNet investigation has discovered. Many users reported that hackers were accessing their accounts, logging them out of all devices, and then changing the account's email and password, effectively taking over the account and locking the previous owner out.
One Main Cause Of Hacked Accounts
Hacked users that were asked if they had re-used existing passwords (sheepishly) admitted that this was indeed the case. Yes, there were also incidents of machines compromised with key-loggers and there probably also have been simply automated attacks using known, hacked popular passwords.
Warn Your Users They Should Not Re-Use Any Passwords, And Especially Not Any Password They Use At The Office
Password re-use is a massive problem. Many of these are already hacked and available for credential-stuffing attacks. It's pretty much like taking candy from a baby at that point.
I suggest you send the following to your employees, friends and family. Feel free to copy/paste/edit:
ALERT: Bad guys are stealing brand new Disney+ accounts. They are doing this mostly by trying to get into accounts using known, hacked usernames and passwords. Many people use the same passwords for many or all their websites. This is very dangerous to do, because if one gets hacked, they all are. Remember to never use the same password for your personal sites, but never ever use any password you use in the office for other things on the internet!
Let's stay safe out there.
Warm regards,
Stu Sjouwerman,
Founder and CEO, KnowBe4, Inc.

PS: Here are 22 more fresh tips to share with your users from our recent National Cyber Security Awareness Month.
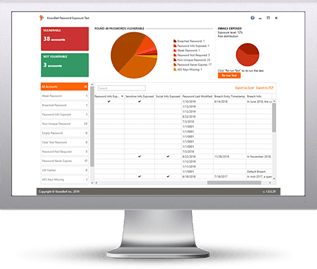 Here's how the Password Exposure Check works:
Here's how the Password Exposure Check works:




