GOVERNANCE, RISK & COMPLIANCE
New-School Compliance Training to Overcome the Problem of Non-Compliance
Our fresh, engaging, regularly updated compliance training content equips your users with the knowledge and awareness they need to comply with regulatory laws, protect themselves from unprofessional and unsafe work environments and safeguard your organization’s reputation.
An Expansive Array of Engaging Content
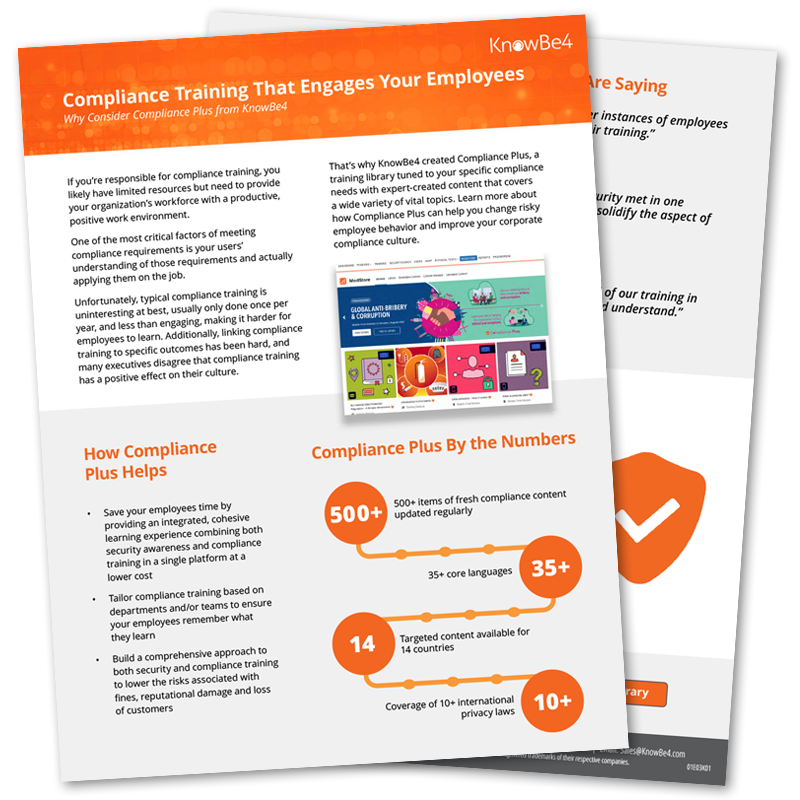
Toss out boring, forgettable checkbox training and start delivering concise, memorable content that changes behavior and reduces risk. Our Compliance Plus training library includes 500+ items of fresh, engaging and regularly updated compliance training content.
Compliance & Regulations Training
Compliance Plus offers full coverage for legislative and data privacy requirements, such as HIPAA, PCI, GDPR and many others.
Customizable Content
With Compliance Plus, you can incorporate your organization’s unique policies and procedures into our new-school, high-quality brandable modules and upload your SCORM-compliant training and video content to the KnowBe4 LMS.
Learning Aids
Supplemental learning aids—such as newsletters, documents and posters—are all included.
Campaigns
When you combine the power of the KnowBe4 platform with Compliance Plus, your organization can set up a fully automated compliance training program in minutes. Additionally, Campaigns comes with world-class support and extensive reporting.
Hear from Peers Who Are Driving Compliance Success
KnowBe4’s Compliance Plus is the only training I have used that doesn’t feel like you are reading or watching content from the 20th century.
Financial services company
The KnowBe4 compliance training is a 10 out of 10. It’s easy, efficient and integrates seamlessly with our security awareness training.
Manufacturing company
KnowBe4’s Compliance Plus training content quality is outstanding.
Financial services company
Preview the Compliance Plus Content Library
Access our ModStore Preview Portal to see the 400+ pieces of content that Compliance Plus has to offer.